Data Leakage in Machine Learning: A Critical Guide for Reliable Environmental Contaminant Research
This article addresses the critical yet often overlooked challenge of data leakage in machine learning (ML) applications for environmental contaminant research.
Data Leakage in Machine Learning: A Critical Guide for Reliable Environmental Contaminant Research
Abstract
This article addresses the critical yet often overlooked challenge of data leakage in machine learning (ML) applications for environmental contaminant research. Aimed at researchers, scientists, and professionals, it provides a comprehensive framework covering the foundational concepts of data leakage, its impact on the validity of models predicting the eco-environmental risks of emerging contaminants, and methodological best practices for its prevention. The content further delves into advanced troubleshooting techniques for detecting leakage and offers robust validation strategies to ensure model reproducibility and real-world applicability, ultimately guiding the development of trustworthy, data-driven environmental insights.
What is Data Leakage? Foundational Concepts and Critical Risks in Environmental ML
In the field of machine learning, particularly in scientific domains such as environmental contaminant research, the integrity of the predictive modeling process is paramount. Data leakage represents a critical threat to this integrity, occurring when information from outside the training dataset—typically from the test set—is used to create the model [1]. This breach in protocol causes a model to appear highly accurate during training and validation phases, only to fail dramatically when deployed in real-world scenarios where future data is genuinely unseen [1]. The consequences extend beyond poor performance to include flawed scientific insights, misallocated resources, and compromised decision-making in critical environmental and health applications.
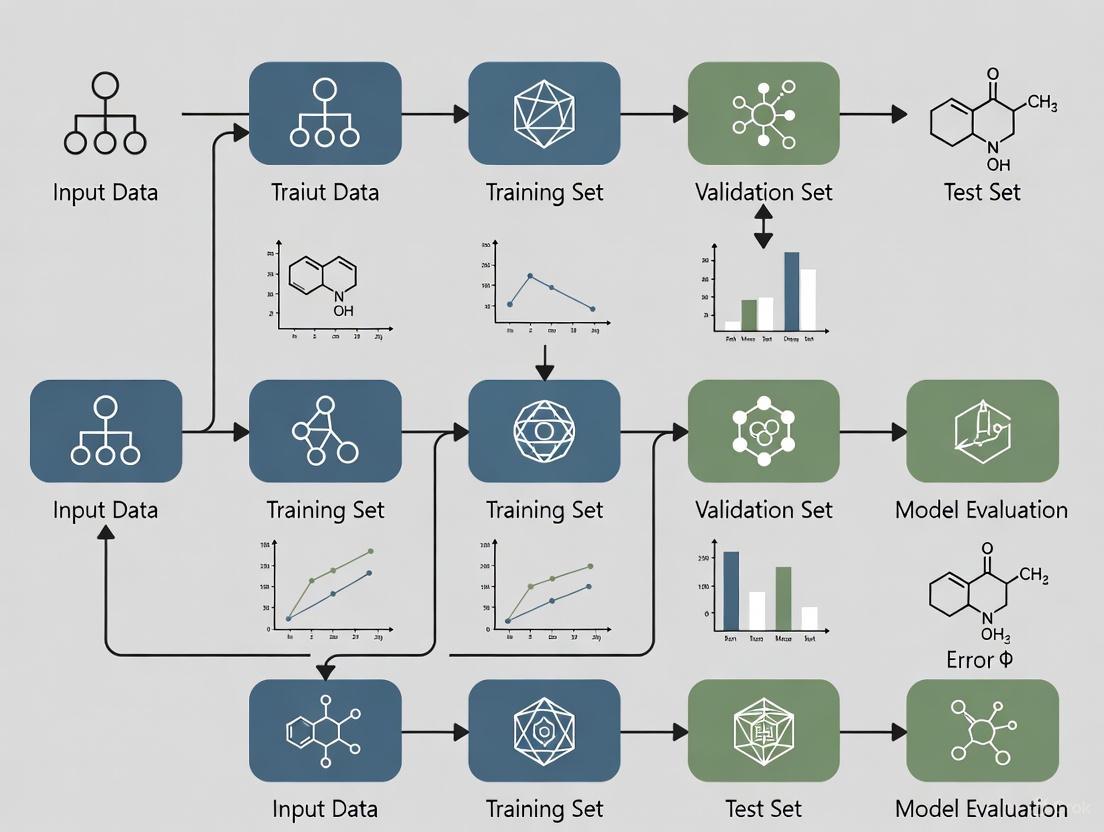
The fundamental purpose of predictive modeling is to create systems that can generalize to new, unseen data. To simulate this real-world condition, the established practice involves splitting available data into separate sets for training and validation [1]. Data leakage violates this core principle by blurring the boundary between what the model should learn from and what it should genuinely predict. In environmental contaminant research, where models may be used to forecast pollution levels or identify contamination sources, data leakage can lead to dangerously inaccurate assessments that undermine public health interventions and policy decisions.
Types and Mechanisms of Data Leakage
Data leakage manifests in several distinct forms, each compromising the model validation process through different mechanisms. Understanding these categories is essential for developing effective prevention strategies.
Target Leakage
Target leakage occurs when models incorporate data that would not be available at the time of prediction in a real-world deployment scenario [1]. This type of leakage creates an unrealistic relationship between features and the target variable, teaching the model to exploit information it wouldn't normally have access to.
A classic example involves credit card fraud detection. A model trained with a "chargeback received" column would appear highly accurate during validation because chargebacks almost always indicate confirmed fraud [1]. However, in practice, a chargeback typically occurs after fraud has been detected and would not be available when the system needs to make a real-time decision on whether to block a transaction. When deployed without this future information, the model's performance degrades significantly [1].
Train-Test Contamination
Train-test contamination arises when the separation between training and validation data is compromised, often during improper data splitting or preprocessing procedures [1]. This form of leakage can be subtle and unintentional, making it particularly dangerous in complex research pipelines.
A common manifestation occurs when standardization or normalization of numerical features is applied to the entire dataset before splitting into training and test sets [1]. When this happens, the model indirectly "sees" information from the test set during training because the preprocessing parameters (mean, standard deviation) were calculated using the complete dataset. The result is artificially inflated performance on the test set, as the model has effectively received prior knowledge about the distribution of the validation data [1].
Specialized Leakage in Scientific Research
In research domains such as neuroimaging and environmental science, additional specialized forms of leakage have been identified:
- Feature selection leakage: Selecting features or brain areas of interest from the entire pool of data rather than from the training data only [2] [3].
- Repeated subject leakage: When data from the same individual appears in both training and testing sets, particularly problematic in longitudinal studies or datasets with family members [2] [3].
- Covariate-related leakage: Performing covariate regression or site correction across the entire dataset before splitting rather than within the cross-validation folds [3].
Table 1: Categories and Characteristics of Data Leakage
| Leakage Type | Definition | Common Causes | Primary Impact |
|---|---|---|---|
| Target Leakage | Inclusion of future/unavailable information during training | Improper feature selection; causal misunderstanding | Overfitting to unrealistic patterns |
| Train-Test Contamination | Breach of separation between training and validation data | Preprocessing before splitting; improper cross-validation | Artificially inflated performance metrics |
| Feature Selection Leakage | Selecting features using complete dataset statistics | Dimensionality reduction on full dataset; biomarker identification prior to splitting | Significant performance inflation, especially in low-signal domains |
| Subject-Level Leakage | Non-independent observations between training and test sets | Repeated measurements; family members in different sets; data duplication | Invalid generalizability claims; reduced reproducibility |
Quantitative Impact of Data Leakage
Recent empirical studies have quantified the dramatic effects of data leakage on model performance across different domains and data types.
Neuroimaging Case Study
A comprehensive 2023 study evaluated the effects of multiple leakage types on connectome-based machine learning models across four large datasets (ABCD, HBN, HCPD, PNC) and three phenotypes (age, attention problems, matrix reasoning) [3]. The research employed over 400 different pipelines to systematically assess how various forms of leakage impact prediction performance, as measured by Pearson's correlation (r) and cross-validation R² (q²) [3].
Table 2: Quantitative Impact of Data Leakage on Model Performance (HCPD Dataset)
| Leakage Type | Impact on Attention Problems | Impact on Age Prediction | Impact on Matrix Reasoning |
|---|---|---|---|
| No Leakage (Baseline) | r=0.01, q²=-0.13 | r=0.80, q²=0.63 | r=0.30, q²=0.08 |
| Feature Leakage | Δr=+0.47, Δq²=+0.35 | Δr=+0.03, Δq²=+0.05 | Δr=+0.17, Δq²=+0.13 |
| Subject Leakage (20%) | Δr=+0.28, Δq²=+0.19 | Δr=+0.04, Δq²=+0.07 | Δr=+0.14, Δq²=+0.11 |
| Leaky Covariate Regression | Δr=-0.06, Δq²=-0.17 | Δr=-0.02, Δq²=-0.03 | Δr=-0.09, Δq²=-0.08 |
| Family Leakage | Δr=+0.02, Δq²=0.00 | Δr=0.00, Δq²=0.00 | Δr=0.00, Δq²=0.00 |
The findings reveal several critical patterns. First, the magnitude of performance inflation is inversely related to baseline performance—models with weaker baseline performance (like attention problems with r=0.01) showed dramatically greater inflation from leakage than strong baseline models (like age prediction with r=0.80) [3]. This pattern is particularly concerning for environmental contaminant research, where true effect sizes may be modest and signals subtle.
Second, not all leakage inflates performance; some forms actually degrade it. Leaky covariate regression consistently decreased prediction performance across all phenotypes [3]. This demonstrates that leakage can produce both optimistically biased performance measures (hindering reproducibility) and pessimistic ones (obscuring true effects).
Brodomain Implications
A National Library of Medicine study found that across 17 different scientific fields where machine learning methods have been applied, at least 294 scientific papers were affected by data leakage, leading to overly optimistic performance reports [1]. This widespread occurrence highlights the systemic nature of the problem and the need for heightened awareness and prevention measures across scientific disciplines, including environmental research.
Detection and Prevention Methodologies
Experimental Protocols for Leakage Detection
Establishing rigorous experimental protocols is essential for identifying and preventing data leakage in research workflows. The following methodologies, adapted from empirical studies, provide a framework for maintaining data integrity:
Protocol 1: Proper Cross-Validation for Temporal Data For time-series environmental data (e.g., contaminant concentration measurements), standard random splitting violates temporal dependencies. Instead, use:
- Chronological splitting: Ensure training data always precedes test data temporally [1]
- Rolling window validation: Train on window [t-n, t-1], test at time t, then increment [1]
- Walk-forward validation: Expand training window while maintaining temporal sequence [1]
- Seasonal adjustment: Account for periodic patterns when creating splits to prevent seasonal information leakage
Protocol 2: Feature Selection Safeguards Based on findings that feature leakage causes significant performance inflation [3]:
- Perform all feature selection, including dimensionality reduction and biomarker identification, strictly within training folds
- Apply selection results (e.g., feature subsets, transformation parameters) to validation data without re-computation
- For neuroimaging and environmental sensor data, select regions of interest or significant sensors using training data only [2]
- Document all feature selection procedures with explicit mention of how training-test separation was maintained
Protocol 3: Preprocessing Integrity Verification To prevent train-test contamination during data preprocessing [1]:
- Fit preprocessing transformations (scaling, normalization, imputation) exclusively on training data
- Apply the fitted transformers to validation data without refitting
- For multi-site studies, calculate and apply site-correction parameters within training folds only [3]
- Validate preprocessing independence by testing whether transformation parameters differ when calculated on full dataset versus training data only
The Researcher's Toolkit: Essential Safeguards Against Leakage
Table 3: Research Reagent Solutions for Preventing Data Leakage
| Tool/Category | Function | Implementation Examples |
|---|---|---|
| Stratified & Time Series Splitters | Creates data splits preserving distributional characteristics or temporal relationships | StratifiedKFold, TimeSeriesSplit (Scikit-learn), GroupShuffleSplit for dependent data |
| Pipeline Constructs | Encapsulates preprocessing and modeling steps to prevent cross-validation contamination | Pipeline and ColumnTransformer (Scikit-learn), tf.data.Dataset (TensorFlow) |
| Data Provenance Trackers | Monitors data lineage and transformation history across experimental iterations | MLflow, Weights & Biases, DVC (Data Version Control), custom experiment trackers |
| Model Validation Suites | Comprehensive performance assessment with leakage detection capabilities | cross_validate (Scikit-learn), check_estimator for protocol verification, custom sanity checks |
| Domain-Specific Splitting Utilities | Handles specialized data dependencies (family, longitudinal, geographic) | GroupKFold for subject independence, LeaveOneGroupOut, spatial blocking for environmental data |
Red Flags and Diagnostic Indicators
Several indicators can signal potential data leakage during model development:
- Unusually high performance: Models showing significantly higher accuracy, precision, or recall than expected, especially on validation data [1]
- Discrepancies between training and test performance: Minimal gap between training and validation performance metrics may indicate contamination [1]
- Inconsistent cross-validation results: High variance across folds or performance that seems too consistent may indicate improper splitting [1]
- Unexpected feature importance: Heavy reliance on features that don't align with domain knowledge or would be unavailable during real-world prediction [1]
- Performance degradation on truly unseen data: Significant drop when moving from validation to external test sets or production deployment [1]
Implications for Environmental Contaminant Research
The methodologies and findings from neuroimaging and other fields have direct relevance to machine learning applications in environmental contaminant research. The systematic review of machine learning in air pollution epidemiology reveals parallel challenges and opportunities [4]. As environmental datasets grow in complexity and volume, traditional statistical methods face limitations, creating both the need for machine learning approaches and vulnerability to data leakage pitfalls.
In environmental monitoring applications, several domain-specific leakage risks emerge:
Temporal Leakage in Contaminant Forecasting Predicting future contamination levels based on historical data requires strict chronological splitting. Using future measurements to inform predictions of past events represents a fundamental violation of causal structure that can create seemingly accurate but useless forecasting models.
Spatial Autocorrelation in Geographic Data Environmental measurements from nearby locations are often correlated. Standard random splitting that places adjacent sampling points in both training and test sets can artificially inflate performance by allowing the model to effectively "cheat" through spatial proximity.
Instrumentation and Laboratory Effects When data comes from multiple sensors or analytical techniques, preventing information leakage about measurement characteristics across splits is essential. Correcting for batch effects or sensor calibration must be performed within training data only.
Transferring the prevention protocols from neuroimaging to environmental contexts requires adapting the core principles while respecting domain-specific data structures. The workflow for environmental contaminant prediction would maintain the same rigorous separation but account for spatial and temporal dependencies unique to ecological systems.
Data leakage represents a fundamental challenge to the validity and reproducibility of machine learning models in scientific research, including environmental contaminant studies. The empirical evidence demonstrates that leakage can dramatically inflate—or in some cases deflate—performance metrics, leading to incorrect conclusions about model capability and potentially flawed real-world decisions.
The most effective approach to data leakage is comprehensive prevention through rigorous experimental design:
- Maintain strict separation between training and test data throughout the entire pipeline, from preprocessing through model evaluation
- Implement temporal and spatial splitting protocols that respect the inherent dependencies in environmental data
- Use pipeline constructs that encapsulate all data transformations and ensure they are fitted only on training data
- Apply domain expertise to scrutinize feature selections and model interpretations for realistic relationships
- Maintain healthy skepticism toward unexpectedly high performance and validate findings through multiple approaches
As machine learning applications in environmental research continue to expand, establishing and adhering to leakage prevention protocols becomes increasingly critical for producing reliable, actionable scientific insights. The methodologies and safeguards outlined provide a foundation for developing more robust predictive models that can genuinely advance our understanding and management of environmental contaminants.
The reproducibility crisis refers to the growing accumulation of published scientific findings that other researchers are unable to reproduce, striking at the core credibility of scientific knowledge [5]. This phenomenon, also termed the replicability crisis, represents a fundamental challenge across numerous scientific disciplines, undermining the reliability of theories built upon irreproducible results and potentially calling substantial portions of scientific knowledge into question [5]. While frequently discussed in relation to psychology and medicine, data strongly indicate that many other natural and social sciences are similarly affected [5].
The crisis gained prominence in the early 2010s through a series of pivotal events that exposed methodological flaws across fields [5]. These included failed replications of highly-cited social priming studies, controversial experiments on extrasensory perception that utilized common but flawed statistical practices, and alarming reports from biotech companies Amgen and Bayer Healthcare indicating replication rates of only 11-20% for landmark findings in preclinical cancer research [5]. Concurrently, metascience studies revealed how widespread questionable research practices—such as exploiting flexibility in data collection and analysis—dramatically increased false positive rates [5].
The machine learning (ML) field faces particular reproducibility challenges, with researchers often spending weeks attempting to reproduce "state-of-the-art" results from top-tier papers without success, frequently hampered by missing code, unspecified random seeds, and unresponsive authors [6]. This crisis represents not merely a technical failure but a systemic issue threatening the scientific enterprise's credibility, especially as data-driven approaches increasingly replace or assist traditional laboratory studies across fields like environmental science [7].
Defining the Scope: Reproducibility vs. Replicability
Within the reproducibility crisis discourse, terminological precision is crucial. Although sometimes used interchangeably, reproducibility and replicability represent distinct concepts with important technical differences [5] [8]:
Reproducibility refers to reexamining and validating the analysis of a given set of data, essentially obtaining the same or similar results when rerunning analyses from previous studies using the original design, data, and code [5] [8].
Replicability involves repeating an existing experiment or study with new, independent data to verify the original conclusions, obtaining similar results when repeating, in whole or part, a prior study [5] [8].
Researchers further categorize replication attempts into several distinct types [5]:
- Direct or exact replication: The experimental procedure is repeated as closely as possible to the original study.
- Systematic replication: The experimental procedure is largely repeated but with some intentional changes to specific parameters.
- Conceptual replication: The finding or hypothesis is tested using a completely different procedure or methodology.
The scientific method operationalizes objectivity through replication, serving as proof that knowledge can be separated from the specific circumstances (time, place, or persons) under which it was originally gained [5]. The inability to achieve consistent results through these processes therefore strikes at the very heart of scientific epistemology.
Quantitative Evidence of the Crisis Across Disciplines
Empirical studies across multiple fields reveal alarming rates of irreproducibility, though estimates vary considerably by discipline and methodology. The following table summarizes key findings from large-scale replication efforts:
Table 1: Reproducibility Rates Across Scientific Disciplines
| Field | Reproducibility Rate | Study Details | Year |
|---|---|---|---|
| Cancer Biology (Bayer Healthcare) | ~34% | Replication of published pre-clinical studies before drug development programs | 2011 [9] |
| Cancer Biology (Amgen) | ~11% | Replication of landmark pre-clinical cancer studies | 2012 [9] |
| Psychology | 36-68% | Large-scale collaborative replication projects (Many Labs) | 2011-2015 [5] [8] |
| Biomedical Research | ~50% | More recent systematic assessment | ~2024 [9] |
| Economics & Social Sciences | 30-70% | Various many-lab replication projects | 2010-2018 [8] |
Beyond these direct replication attempts, survey evidence further illustrates the pervasiveness of the problem. A Nature survey conducted in 6 found that between 60-80% of scientists across various disciplines reported encountering hurdles in reproducing their peers' work, with 40-60% experiencing difficulties replicating their own experiments [8]. It is important to note, however, that some scholars question the existence of a full-blown "crisis," pointing to the lack of conclusive evidence quantifying its true scale and arguing that the current approach to addressing it may not adhere to the rigorous standards normally applied to the scientific method [10].
A Case Study in Machine Learning and Environmental Contaminant Research
The field of environmental contaminant research exemplifies both the promise and pitfalls of data-driven science, particularly as machine learning approaches increasingly replace or supplement traditional laboratory studies [7] [11]. Research on emerging contaminants (ECs)—such as antibiotics, microplastics, and PFAS—faces specific data science challenges that exacerbate reproducibility concerns [7] [11].
Common Data Issues in Contaminant Research
Table 2: Data Science Challenges in Environmental Contaminant Research
| Challenge | Impact on Reproducibility | Potential Solutions |
|---|---|---|
| Matrix Influence | Effects of complex environmental matrices on contaminant behavior are often ignored, limiting real-world applicability [7]. | Develop ensemble models that account for complex environmental interactions [7]. |
| Trace Concentration | Low concentration detection and effect prediction create signal-to-noise issues in ML models [7]. | Implement specialized detection algorithms and validation protocols. |
| Complex Scenarios | Oversimplified laboratory conditions fail to capture environmental complexity [7]. | Create integrated research frameworks combining lab and field studies [7]. |
| Data Leakage | Inadvertent sharing of information between training and test sets creates overly optimistic performance metrics [7]. | Implement rigorous validation schemes and preprocessing pipelines. |
Exemplary Approach: ML for High Voltage Insulator Contamination
A 2025 study on contamination classification of polluted high voltage insulators using leakage current demonstrates a robust methodological approach that addresses several reproducibility challenges [12]. This research developed a meticulous dataset under controlled laboratory conditions while incorporating critical parameters of temperature and varying humidity to reflect real-world environmental impact [12]. The methodology included:
- Dataset Generation: Artificially polluted insulators divided into three contamination classes (high, moderate, low) with leakage current measurements under varied environmental conditions [12].
- Feature Extraction: Comprehensive preprocessing and feature extraction from time, frequency, and time-frequency domains, with feature ranking to identify the most important variables [12].
- Model Optimization: Four distinct ML models (including decision trees and neural networks) trained using Bayesian optimization for parameter tuning [12].
Notably, this study achieved accuracies consistently exceeding 98%, with decision tree-based models exhibiting significantly faster training and optimization times compared to neural network counterparts [12]. This research exemplifies how carefully controlled data collection and processing can produce highly reproducible results even in complex environmental applications.
Experimental Protocols for Reproducible Research
Detailed Methodology: Leakage Current Experiment
The experimental protocol from the high-voltage insulator contamination study provides a template for reproducible research design in ML-driven environmental applications [12]:
1. Sample Preparation
- Porcelain insulators were artificially polluted according to standardized contamination protocols
- Three distinct contamination classes were established: high, moderate, and low contamination
- Contamination levels were quantitatively verified through direct measurement
2. Data Collection Under Controlled Conditions
- Leakage current measurements were taken under systematically varied laboratory conditions
- Critical environmental parameters (temperature, humidity) were precisely controlled and documented
- Multiple trials were conducted for each contamination class under identical conditions
3. Data Preprocessing Pipeline
- Raw leakage current signals were processed to remove artifacts and noise
- Data were normalized to account for experimental variations
- Dataset was partitioned using strict separation between training, validation, and test sets
4. Feature Extraction and Selection
- Features were extracted from multiple domains: time, frequency, and time-frequency
- Extracted features were ranked by importance using statistical methods
- Most predictive features were selected for model training
5. Model Training with Bayesian Optimization
- Four ML models were trained: decision trees, neural networks, and others
- Bayesian optimization technique was systematically applied to hyperparameter tuning
- Performance was evaluated using multiple metrics: accuracy, precision, recall, F1-score
Research Reagent Solutions
Table 3: Essential Materials for Reproducible ML-Environmental Research
| Research Reagent | Function in Experimental Protocol | Specifications for Reproducibility |
|---|---|---|
| Porcelain Insulators | Standardized test subject for contamination studies | Identical material composition and surface properties [12] |
| Contamination Simulants | Artificially reproduce environmental pollutant deposition | Precise chemical composition and concentration documentation [12] |
| Leakage Current Sensors | Measure electrical current flow across insulator surfaces | Calibration certification and measurement frequency specifications [12] |
| Environmental Chambers | Control temperature and humidity during experiments | Precision control parameters (±0.5°C, ±2% RH) and validation records [12] |
| Feature Extraction Algorithms | Convert raw signals into analyzable features | Code availability with version control and dependency documentation [12] |
Visualization of Research Workflows and Relationships
The following diagrams illustrate key experimental workflows and conceptual relationships in reproducible research, created using Graphviz DOT language with the specified color palette.
Research Workflow for Environmental ML
Crisis Root Causes and Solutions
Solutions and Emerging Approaches
Addressing the reproducibility crisis requires multi-faceted interventions targeting various stages of the research lifecycle. Promising approaches include:
Open Science Practices
Systematic adoption of open science practices represents one of the most promising avenues for improving reproducibility [8]. These include:
- Data and Code Sharing: Making datasets and analysis code publicly available enables other researchers to verify and build upon existing work [8].
- Study Preregistration: Registering study designs, hypotheses, and analysis plans before data collection reduces questionable research practices [8].
- Open Access Publishing: Making research findings freely available ensures broader scrutiny and validation [13].
However, evidence for the effectiveness of these interventions remains limited. A 2025 scoping review found that of 105 studies examining interventions to improve reproducibility, only 15 directly measured the effect on reproducibility or replicability, with the remainder addressing proxy outcomes like data sharing or methods transparency [8]. Moreover, 30 studies were non-comparative and 27 used cross-sectional observational designs that preclude causal inference [8].
Specialized Reproducibility-Focused Venues
New scholarly venues are emerging with reproducibility as a core principle. Computo, for example, is a journal for transparent and reproducible research in statistics and machine learning that requires submissions to be formatted as executable notebooks integrating text, code, equations, and references [13]. Each submission must be associated with a git repository configured to demonstrate dynamic and durable reproducibility of the contribution [13].
Computo distinguishes between "editorial reproducibility" (the ability to re-run provided code and obtain the same outputs) and "scientific reproducibility" (the robustness and generalizability of findings), acknowledging that complex fields like deep learning present unique challenges for reproducibility standards [13].
Community-Led Initiatives
The machine learning community has developed specific initiatives to address reproducibility, such as the Machine Learning Reproducibility Challenge, a conference venue for sharing reproducible methods and tools, investigating the reproducibility of papers from top conferences, and testing the generalizability of scientific findings through novel insights and empirical results [14].
These community efforts acknowledge that reproducibility in ML is often a "heroic act" that is "not efficient, not legal, not credited," as noted by Soumith Chintala of Meta in a keynote address [14], highlighting the systemic barriers to reproducible research even when technical solutions exist.
The reproducibility crisis affects a broad spectrum of scientific fields, from psychology and medicine to machine learning and environmental science. Quantitative evidence from large-scale replication efforts reveals concerning rates of irreproducibility, though precise estimates vary by discipline. The crisis stems from multiple root causes, including questionable research practices, insufficient methodological training, and a pervasive publish-or-perish culture that often prioritizes novel findings over robust verification.
The case of machine learning applications in environmental contaminant research illustrates both the specific challenges and potential solutions. Data leakage, matrix effects, and oversimplified experimental scenarios can compromise reproducibility, while careful study design, comprehensive feature engineering, and robust validation protocols can enhance it. Emerging approaches centered on open science, specialized reproducible research venues, and community-led initiatives offer promising paths forward.
Addressing the reproducibility crisis requires concerted effort across the scientific ecosystem—funders, institutions, publishers, and individual researchers all have roles to play in creating incentives for reproducibility and providing the tools and training necessary to achieve it. As scientific research grows increasingly complex and data-driven, ensuring the reliability and verifiability of published findings becomes ever more critical to maintaining public trust and advancing knowledge.
The application of machine learning (ML) to environmental contaminant research represents a paradigm shift in how scientists monitor, assess, and mitigate ecological threats. However, this promising intersection faces fundamental data vulnerability challenges that threaten the validity and real-world applicability of research findings. Environmental data possesses inherent characteristics—complex scenarios and trace concentrations—that create unique obstacles for ML workflows. These vulnerabilities are particularly problematic within the context of data leakage, where information from outside the training dataset inadvertently influences the model, creating overly optimistic performance metrics that fail to generalize to real-world conditions [7]. The matrix effect, where complex environmental matrices interfere with contaminant detection and quantification, further compounds these challenges by introducing systematic biases that can be amplified by ML algorithms [7] [11]. This technical analysis examines the core vulnerabilities of environmental data within ML workflows and proposes methodological frameworks to enhance research rigor.
Fundamental Vulnerabilities in Environmental Data
The Challenge of Complex Environmental Scenarios
Environmental systems operate as interconnected networks of biological, chemical, and physical processes that create multidimensional complexity difficult to capture in ML models. The integrated research framework encompassing natural fields, ecological systems, and large-scale environmental problems is often compromised when models are trained solely on simplified laboratory data [7]. This disconnect between training data and real-world complexity manifests in several critical ways:
Spatiotemporal Heterogeneity: Environmental contaminants distribute unevenly across landscapes and water bodies, with concentrations fluctuating based on seasonality, weather patterns, and anthropogenic activities. ML models trained on limited spatial or temporal data fail to capture these dynamics, leading to inaccurate predictions when applied to new contexts or timeframes [7].
Multivariate Interactions: Contaminants rarely exist in isolation; they interact with other compounds, environmental media, and biological systems in ways that alter their behavior, toxicity, and detectability. Most ML approaches struggle to model these higher-order interactions, especially when training data comes from reductionist laboratory studies that control for environmental variables [11].
Ecological System Complexity: The transition from controlled laboratory conditions to natural ecosystems introduces countless confounding factors—from microbial communities to sediment characteristics—that significantly impact contaminant fate and transport but are rarely comprehensively included in ML training datasets [7].
The Analytical Precision Problem at Trace Concentrations
Emerging contaminants (ECs) frequently exist in the environment at concentrations that push against the detection limits of analytical instrumentation, creating fundamental data quality challenges for ML applications. The trace concentration problem manifests across multiple dimensions of the ML pipeline [7]:
Signal-to-Noise Ratio Limitations: At part-per-billion or part-per-trillion levels, instrumental signals for target contaminants approach the noise floor of detection systems, creating inherent uncertainty in the training data itself. ML models trained on these noisy measurements may learn to amplify analytical artifacts rather than true environmental patterns.
Matrix Interference Effects: The presence of co-extracted compounds in environmental samples can suppress or enhance analyte signals, leading to inaccurate quantification. When these matrix influence effects are not consistent across samples, they introduce non-systematic errors that ML algorithms cannot easily distinguish from true concentration variations [7].
Censored Data Challenges: Measurements below method detection limits create left-censored datasets that require specialized statistical handling before they can be utilized in ML workflows. Common approaches (e.g., substitution with MDL/2) can introduce bias that propagates through the modeling process, particularly when censoring levels are high [11].
Table 1: Data Vulnerability Framework for Environmental ML Applications
| Vulnerability Category | Technical Manifestation | Impact on ML Model Performance |
|---|---|---|
| Complex Scenarios | Disconnect between laboratory training data and field conditions | Poor generalization to real-world environments; inaccurate spatial predictions |
| Trace Concentrations | High measurement uncertainty near detection limits | Reduced predictive accuracy; amplification of analytical noise |
| Matrix Effects | Signal suppression/enhancement from co-occurring substances | Systematic bias in concentration predictions; inaccurate source attribution |
| Spatiotemporal Dynamics | Non-stationary contamination patterns across space and time | Model degradation when applied to new locations or time periods |
| Multivariate Interactions | Unmeasured confounding variables in environmental systems | Omitted variable bias; incorrect causal inference |
The Data Leakage Crisis in Environmental ML Research
Mechanisms of Data Leakage in Environmental Contexts
Data leakage represents a critical threat to the validity of ML applications in environmental science, often creating an illusion of model performance that disintegrates when deployed in real-world settings. In the context of environmental contaminants, leakage occurs when information from outside the training dataset influences model development, typically through improper separation of data that should remain independent. The ensemble models designed to reveal mechanisms and spatiotemporal trends must be developed without data leakage to maintain their validity and predictive power [7]. Several specific leakage mechanisms plague environmental ML research:
Temporal Leakage: Using future data to predict past contamination events represents a fundamental violation of temporal causality common in environmental forecasting. For example, training models on water quality parameters that incorporate seasonal variation without proper time-series splitting can lead to inflated performance metrics that fail to manifest in actual forecasting scenarios [15].
Spatial Autocorrelation: Environmental data points collected from proximity to one another are typically more similar than distant points, violating the assumption of independence fundamental to many cross-validation approaches. When spatial dependencies are not properly accounted for during data splitting, models appear to perform well but cannot generalize to new geographic areas [16].
Feature Leakage: Including variables in training that would not be available during actual prediction scenarios creates feature-based leakage. In environmental contexts, this often occurs when using expensive laboratory measurements as predictors for field-deployable sensors or when incorporating downstream effects as predictors for upstream causes [7].
Case Study: Data Leakage in Drinking Water Quality Prediction
Recent research applying ML to predict drinking water quality in California demonstrates how modeling decisions can introduce leakage with significant environmental justice implications. Studies have found that modeling choice transparency is critically important when using ML for environmental justice applications, as optimization parameter choices and classification threshold selections can dramatically affect error distribution across demographic groups [15]. In one analysis, altering classification thresholds changed which communities were most likely to be false negatives—a critical consideration when misclassification could expose vulnerable populations to contaminated water [15]. This exemplifies how technical decisions in the ML pipeline can either exacerbate or mitigate systemic environmental inequalities, moving beyond mere statistical accuracy to consequential real-world impacts.
Methodological Framework for Robust Environmental ML
Experimental Protocols for Vulnerability Mitigation
Implementing rigorous methodological protocols throughout the ML pipeline is essential for producing environmentally relevant models that maintain validity under complex real-world conditions. The following experimental frameworks address the core vulnerabilities of environmental data:
Integrated Validation Framework: Establish a multi-tiered validation approach incorporating (1) hold-out testing with strict spatiotemporal segregation, (2) external validation using completely independent datasets from different geographic regions or time periods, and (3) field validation comparing predictions with actual environmental measurements collected specifically for model verification purposes [7] [11].
Causal Relationship Development: Prioritize strong causal relationships in model development through incorporation of domain knowledge, mechanistic understanding, and causal inference techniques rather than relying solely on correlational patterns that may reflect spurious relationships or unmeasured confounding [7].
Uncertainty Quantification Protocol: Implement comprehensive uncertainty propagation that accounts for analytical measurement error, spatial interpolation uncertainty, and model parameter uncertainty, providing decision-makers with probabilistic predictions rather than point estimates, which is especially critical for trace-level contaminants [11].
Table 2: Research Reagent Solutions for Environmental ML Workflows
| Research Reagent | Technical Function | Application in Environmental ML |
|---|---|---|
| Ensemble Models | Combines multiple algorithms to improve predictive performance and robustness | Reduces variance in predictions; handles complex nonlinear relationships in environmental data |
| Explainable AI (XAI) | Provides interpretable insights into model decisions and feature importance | Identifies key drivers of contamination; builds regulatory trust in model outputs |
| Spatiotemporal Cross-Validation | Preserves data structure during model evaluation | Prevents data leakage from spatial autocorrelation and temporal autocorrelation |
| Censored Data Handling | Specialized statistical methods for values below detection limits | Maintains data integrity for trace-level contaminants without introducing bias |
| Multi-Modal Data Fusion | Integrates disparate data types (remote sensing, field measurements, laboratory assays) | Captures environmental complexity; improves model comprehensiveness |
Visualization of Environmental ML Workflow and Vulnerabilities
Environmental ML Vulnerability and Mitigation Workflow
Data Leakage Prevention Protocol
Data Leakage Prevention Protocol in Environmental ML
The vulnerabilities inherent in environmental data—particularly complex scenarios and trace concentrations—represent significant but surmountable challenges for machine learning applications. Addressing these issues requires moving beyond predictive accuracy as the sole metric of model success toward a more comprehensive framework that prioritizes causal understanding, real-world applicability, and equity considerations. The mutual inspiration among data science, process and mechanism models, and laboratory and field research emerges as a critical pathway forward, ensuring that ML applications remain grounded in environmental reality rather than mathematical abstraction [7]. As the field continues to evolve, researchers must maintain rigorous standards for data quality, model transparency, and validation protocols to ensure that machine learning fulfills its potential as a tool for environmental protection rather than a source of misleading conclusions. By directly confronting the vulnerabilities outlined in this analysis, the environmental ML community can develop more robust, reliable, and equitable applications that effectively address the pressing challenge of environmental contamination.
In environmental contaminant research, data leakage represents a critical methodological pitfall that occurs when information from outside the training dataset is inadvertently used to create a model. This flaw produces overoptimistic performance metrics during development that vanish when the model encounters real-world data, leading to dangerously inaccurate environmental decisions [17]. The consequences are particularly severe in fields like contaminant prediction and risk assessment, where model outputs directly influence public health interventions and multi-million-dollar remediation strategies. This technical guide examines the origins and impacts of data leakage in machine learning (ML) for environmental science, providing researchers with robust detection and prevention methodologies to ensure model reliability and regulatory compliance.
The Data Leakage Problem in Environmental Research
Fundamental Concepts and Definitions
Data leakage in machine learning refers to the erroneous incorporation of information from outside the training dataset during model development, creating an unrealistic advantage that inflates performance estimates. This problem manifests through two primary mechanisms:
Feature Leakage: When datasets contain features that would not be available at the time of prediction in a real-world deployment scenario. In environmental monitoring, this might include using future contaminant concentration measurements to predict current levels or incorporating data from remediation sites that would not be available for uncontaminated locations.
Temporal Leakage: Particularly prevalent in time-series environmental data, this occurs when future observations influence the training of models intended for forecasting. For spatiotemporal contamination models predicting hexavalent chromium distributions, using data from multiple time periods without proper temporal segregation creates fundamentally flawed validation [18].
Prevalence in Environmental Contaminant Research
Recent bibliometric analyses reveal a concerning acceleration of ML applications in environmental chemical research, with publications surging from fewer than 25 annually before 2015 to over 719 in 2024 alone [16]. This rapid adoption has outpaced the implementation of rigorous methodological safeguards, creating fertile ground for inadvertent data leakage. The analysis of 3,150 peer-reviewed articles identified eight major research clusters, with water quality prediction and quantitative structure-activity relationship (QSAR) modeling among the most prominent domains where leakage frequently occurs [16].
Table 1: Domains Most Vulnerable to Data Leakage in Environmental ML
| Research Domain | Primary Leakage Risks | Typical Consequences |
|---|---|---|
| Water Quality Prediction [17] [16] | Temporal autocorrelation in sensor data; spatial autocorrelation in monitoring wells | Overestimation of prediction accuracy by 15-25% |
| Chemical Risk Assessment [16] | Use of test set chemicals during feature selection | False negative predictions for novel contaminants |
| Groundwater Contamination Forecasting [18] | Improper separation of spatiotemporal data | Faulty remediation planning and resource allocation |
| Environmental Health Risk Modeling [19] | Leakage of demographic or health outcome data into exposure features | Inaccurate identification of high-risk populations |
Case Studies: Leakage Consequences in Environmental Research
Groundwater Contamination Forecasting
At the Hanford 100-Area, a site historically contaminated with hexavalent chromium (Cr[VI]), researchers applied random forest algorithms to predict spatiotemporal contaminant distributions in groundwater [18]. The complex hydrogeology and multiple potential contamination pathways created significant challenges for traditional conceptual site models. The initial modeling approach improperly handled the temporal relationship between river stage fluctuations and contaminant measurements, creating a model that appeared highly accurate during validation but failed to provide reliable predictions for directing pump-and-treat operations. This case exemplifies how spatiotemporal dependencies in environmental systems present particularly subtle leakage pathways that can compromise remediation decisions with significant financial and environmental consequences [18].
Lead Contamination Risk Prediction
In Washington, DC, explainable machine learning models were developed to predict blood lead levels and school drinking water contamination using environmental, topographic, socioeconomic, and infrastructure features [19]. The research team implemented rigorous cross-validation techniques to prevent leakage between distinct geographical areas and between individual-level and community-level data sources. Models achieved exceptional discriminative performance (AUC = 0.90-0.95) specifically because they addressed potential leakage pathways during feature engineering [19]. This case demonstrates that proactive leakage prevention enables the development of reliable tools for prioritizing lead service line replacements and protecting vulnerable populations.
Diagram 1: Data leakage impact cascade (49 characters)
Detection and Prevention Methodologies
Experimental Design Protocols
Preventing data leakage begins with meticulous experimental design that respects the temporal and spatial dependencies inherent in environmental data collection. The following protocols provide robust safeguards:
Temporal Segregation: For time-series contamination data, establish a clear temporal cutoff where all data before a specific date is used for training and all subsequent data is reserved for testing. This approach is essential for groundwater contamination forecasting where seasonal patterns and multi-year trends create autocorrelation [18].
Spatial Blocking: When dealing with geographically distributed sampling (e.g., groundwater monitoring wells, air quality sensors), implement spatial blocking techniques that ensure nearby locations remain in either training or testing sets, preventing models from exploiting spatial autocorrelation as a false signal.
Feature Validation: Rigorously audit each feature to confirm its real-world availability at the time of prediction. For lead contamination risk models, this means verifying that infrastructure data (e.g., pipe material, building age) reflects historical records rather than current assessments [19].
Technical Implementation Framework
Implementing leakage prevention requires both algorithmic strategies and validation methodologies:
Nested Cross-Validation: Employ nested (double) cross-validation where the inner loop performs hyperparameter optimization and the outer loop provides unbiased performance estimation. This approach was successfully applied in assessing China's industrial policy impacts on green economic growth using the double machine learning model [20].
Domain-Aware Splitting: Instead of random data splitting, use knowledge of the environmental domain to create semantically meaningful splits. For school drinking water contamination, this might involve splitting by school district rather than individual schools to prevent leakage of shared infrastructure characteristics [19].
Explainability Audits: Implement SHAP (SHapley Additive exPlanations) or similar interpretability frameworks to identify features with implausibly high predictive power that may indicate leakage [19]. This approach helped researchers validate that lead pipe density and social vulnerability—rather than leaked features—were genuinely driving contamination risk predictions.
Table 2: Leakage Prevention Techniques for Environmental Data Types
| Data Type | Primary Prevention Method | Validation Approach | Tools/Implementations |
|---|---|---|---|
| Time-Series Contamination Measurements [18] | Forward chaining (e.g., TimeSeriesSplit) | Comparison of temporal vs. random split performance | scikit-learn TimeSeriesSplit, custom temporal validators |
| Spatial Environmental Sampling [18] | Spatial blocking with buffer zones | Spatial autocorrelation analysis of residuals | GIS integration, scikit-learn ClusterCrossValidation |
| Structural Environmental Data (e.g., pipe materials) [19] | Temporal validation of feature availability | Domain expert feature audit | Feature documentation protocols, model cards |
| High-Throughput Screening Data [16] | Scaffold splitting based on chemical structure | Performance disparity analysis on novel compounds | RDKit, specialized cheminformatics splitting algorithms |
Diagram 2: Leakage prevention workflow (45 characters)
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Methodological Tools for Leakage Prevention
| Tool/Category | Function | Implementation Example |
|---|---|---|
| Temporal Cross-Validation [18] | Prevents time-based leakage in monitoring data | scikit-learn TimeSeriesSplit with seasonality awareness |
| Spatial Cross-Validation [18] | Addresses spatial autocorrelation in environmental samples | SpatialBlockCV using GIS coordinates of monitoring wells |
| Double Machine Learning [20] | Provides robust causal inference in high-dimensional settings | Orthogonalization for policy impact assessment on green growth |
| Explainable AI (XAI) Frameworks [19] | Identifies leaked features through interpretability | SHAP analysis for lead contamination risk factor identification |
| Chemical Splitting Algorithms [16] | Prevents leakage in QSAR and chemical risk assessment | Scaffold splitting based on molecular structure similarity |
| MLOps Platforms with Carbon Awareness [21] | Ensures reproducible, efficient model training | Kubernetes with autoscaling for lifecycle management |
Data leakage represents a fundamental challenge to the integrity of machine learning applications in environmental contaminant research. The consequences of undetected leakage extend beyond statistical anomalies to directly impact environmental decision-making, remediation resource allocation, and public health protection. As ML adoption accelerates across environmental science, the implementation of rigorous methodological safeguards against data leakage must become standard practice. Through temporal segregation, spatial blocking, domain-aware validation, and explainability audits, researchers can develop models that maintain their validity when deployed in real-world environmental management contexts. The future of trustworthy environmental ML depends on this methodological rigor, ensuring that promising laboratory results translate to genuine field efficacy.
Building Robust Pipelines: Methodological Strategies to Prevent Leakage in Contaminant Analysis
In environmental machine learning, the accurate prediction of phenomena—from contaminant concentrations to ecological shifts—hinges on the integrity of the model validation process. Data leakage, wherein information from the future inadvertently influences the model's understanding of the past, represents a pervasive threat to model validity, leading to overly optimistic performance estimates and models that fail in real-world deployment. This in-depth technical guide addresses the core challenge of implementing temporally correct data splitting for environmental time-series data, framing it within the broader thesis of mitigating data leakage in environmental contaminant research. Unlike traditional random train-test splits, which ignore the intrinsic temporal ordering of observations, methodologies that preserve chronological order are essential for producing reliable, generalizable models that can truly support scientific and regulatory decision-making [22] [23].
The consequences of improper splitting are particularly acute in environmental contexts. For instance, a model predicting NOx concentrations might achieve deceptively high accuracy if trained on a randomly shuffled dataset, as it could subtly memorize short-term patterns that are not causal. When deployed to forecast future pollution events, such a model would likely perform poorly, compromising early warning systems [24]. Similarly, in landslide detection, using satellite imagery from after an event to help identify precursors of that same event constitutes a severe temporal leak, invalidating any assessment of the model's predictive capability [25]. This guide provides researchers, scientists, and development professionals with the experimental protocols and theoretical foundation needed to implement robust temporal splitting, thereby ensuring the development of models that are both scientifically sound and practically useful.
Foundational Concepts: Why Time Series Demand Specialized Splitting
The Problem of Temporal Dependence and Data Leakage
Standard cross-validation techniques, such as K-Fold, operate on the assumption that data points are independently and identically distributed (i.i.d.). In this framework, randomly splitting the data into training and testing subsets is statistically valid. However, time-series data, by its nature, violates this core assumption. Environmental observations collected over time exhibit temporal dependence; the value at time t is often correlated with values at times t-1, t-2, and so on [22].
Applying random splitting to such data creates a fundamental flaw: the model may be trained on data points that chronologically occur after those in its test set. This allows the model to leverage "future" information to "predict" the past, a scenario that is impossible in a real-world forecasting context. This inflates performance metrics and constitutes data leakage, producing a model that has memorized temporal correlations rather than learned underlying causal or systemic patterns [23]. As noted in discussions on time-series cross-validation, "We cannot choose random samples... because it makes no sense to use the values from the future to forecast values in the past" [22].
Core Principles for Temporal Splitting
To avoid these pitfalls, any data splitting strategy for time series must adhere to two key principles established in the literature [22] [23]:
- Chronological Ordering: The training set must always consist of observations that occur strictly before those in the validation or test set. This mimics the real-world forecasting scenario where only past data is available to predict the future.
- Preservation of Temporal Structure: The sequence and dependencies within the data (e.g., seasonality, trends) must be maintained within the training and test sets. Shuffling individual data points destroys this structure and invalidates the model evaluation.
Methodologies for Temporal Data Splitting and Cross-Validation
This section details established experimental protocols for splitting temporal data, progressing from simple single splits to more sophisticated cross-validation techniques.
Single Temporal Split
The most straightforward approach is a single split that reserves a contiguous block of the most recent data for testing.
- Protocol: The dataset is divided into two segments based on a selected point in time. All data before this point is used for training, and all data after is used for testing.
- Use Case: This is suitable for initial model development or when data is abundant. Its main limitation is that the evaluation is based on a single test period, which may not be representative of all temporal variations (e.g., a specific season or anomalous event) [24].
- Implementation: In a 10-year dataset of contaminant concentrations, one might use years 1-8 for training and years 9-10 for testing.
Rolling Origin Cross-Validation (Forward Chaining)
A more robust and widely recommended method is Rolling Origin Cross-Validation, also known as forward chaining or evaluation on a rolling forecasting origin [26] [23]. This method creates multiple training-test splits, providing a more reliable estimate of model performance.
- Protocol: The process starts with a small training set. The model is trained and used to forecast the next period(s), which serve as the test set. These forecasted data points are then incorporated into the training set for the next iteration, and the process repeats, rolling the origin forward [22] [23].
- Use Case: This is the canonical approach for time-series model selection and evaluation, as it effectively simulates the process of making successive forecasts in a live environment [23].
- Implementation Example: For a six-year series, the splits would be [23]:
- Fold 1: Train [1], Test [2]
- Fold 2: Train [1, 2], Test [3]
- Fold 3: Train [1, 2, 3], Test [4]
- Fold 4: Train [1, 2, 3, 4], Test [5]
- Fold 5: Train [1, 2, 3, 4, 5], Test [6]
Time Series Split Cross-Validation
A variant of rolling origin, TimeSeriesSplit (as implemented in libraries like scikit-learn), uses a fixed-size training window that slides through the data, or an expanding window that grows with each fold [22] [27].
- Protocol: The dataset is split into
n_splits + 1segments. For each fold i, the first i segments are used for training, and the (i+1)th segment is used for testing. This ensures the test set is always ahead of the training set [22]. - Use Case: Ideal for evaluating how a model's performance changes as more data becomes available. It is a standardized method that is easy to implement using common programming libraries [27].
- Experimental Workflow: The following diagram illustrates the logical workflow for implementing a time-series cross-validation experiment, from data preparation to performance evaluation.
Advanced and Blocked Methodologies
For more complex scenarios, advanced methodologies offer additional safeguards.
- Nested Cross-Validation: This involves an outer loop for performance estimation and an inner loop for hyperparameter tuning, all while strictly preserving temporal order. This is critical for obtaining unbiased performance estimates when model selection is part of the process.
- Blocked Cross-Validation: Standard rolling windows can still leak information if the model uses lagged features. Blocked cross-validation introduces a gap, or "margin," between the training and validation folds to prevent the model from observing lagged values that are used both as a regressor and a response. A second gap between folds themselves prevents the model from memorizing patterns from one iteration to the next [22].
- Population-Informed Splitting for Multiple Time Series: When the dataset contains independent time series from different sources (e.g., multiple contaminant monitoring stations), the strict temporal ordering can be relaxed between these series. The training set can include all data from other stations, even if it is from a "future" date, because the series are independent. However, temporal order must be preserved within each station's data [22].
Quantitative Comparison of Splitting Methodologies
The table below summarizes the key characteristics, advantages, and limitations of the primary temporal splitting methods discussed.
Table 1: Comparative Analysis of Temporal Data Splitting Methodologies
| Methodology | Core Principle | Key Advantage | Primary Limitation | Ideal Use Case |
|---|---|---|---|---|
| Single Temporal Split | Single contiguous split into past (train) and future (test). | Simple to implement and understand; computationally efficient. | Performance evaluation relies on a single, potentially non-representative, test period. | Initial model prototyping with very large datasets. |
| Rolling Origin (Forward Chaining) | Training set expands to include each test set for the next iteration. | Closely mimics real-world forecasting; provides multiple performance estimates. | Training set size increases over time, conflating performance with data volume. | Robust model evaluation and selection for standard forecasting tasks. |
| Time Series Split (Fixed Window) | Training window of fixed size slides through the data. | Controls for training set size; evaluates performance consistently over time. | Does not utilize all available historical data for training in earlier folds. | Evaluating model performance under a fixed memory constraint. |
| Blocked Cross-Validation | Introduces gaps between training and validation sets. | Mitigates leakage from lagged features and between iterations; highly robust. | Reduces the amount of data available for training and validation. | Models that heavily rely on lagged observations or recurrent architectures. |
| Nested Cross-Validation | Outer loop for evaluation, inner loop for temporal tuning. | Provides unbiased performance estimate when hyperparameter tuning is required. | Computationally very expensive, especially with long time series. | Final model assessment and benchmarking in research publications. |
Case Studies in Environmental Research
Air Pollution Modelling (NOx Concentration)
A study on combined NOx concentration modelling highlights the importance of data splitting, where models using Artificial Neural Networks (ANN) and Random Forests (RF) were able to achieve strong fits (MAPE values of 18.3–18.5%) for predicting NOx levels. The careful structuring of the data, ensuring that models were trained on past data to predict future concentrations, was fundamental to obtaining reliable results that could inform pollution mitigation strategies [24]. The use of meteorological factors and past concentrations as features makes temporal splitting non-negotiable to avoid learning from future conditions.
Landslide Detection with Satellite Imagery
The Sen12Landslides dataset, a large-scale, multi-modal, and multi-temporal resource for satellite-based landslide detection, was explicitly designed to address temporal dynamics. The dataset includes "pre- and post-event timestamps" for landslide events, which are crucial for constructing temporally valid training and testing splits. Benchmark experiments using models like U-ConvLSTM and 3D-UNet, which leverage this temporal information, achieved F1-scores exceeding 83%. This underscores that using single or bi-temporal images can lead to models that misclassify regular land surface changes as landslides, whereas a proper multi-temporal setup allows the model to learn genuine event-based dynamics [25].
Vegetation Leaf Area Index (LAI) Estimation
Research on estimating high spatio-temporal resolution LAI using an Ensemble Kalman Filter-NDVI (ENKF-NDVI) model generated a time series from 2016 to 2022. The validation of this product with ground-based measurements (R² of 0.85, RMSE of 0.39) inherently required a temporal split where the model was trained on earlier data and validated on later periods to confirm its predictive capability for forest planning and management [28].
Implementing robust temporal models requires a suite of computational tools and data resources. The following table details key reagents and their functions in this domain.
Table 2: Key Research Reagent Solutions for Temporal Modeling in Environmental Science
| Tool / Resource | Type | Primary Function | Relevance to Temporal Splitting |
|---|---|---|---|
Scikit-learn (TimeSeriesSplit) |
Python Library | Provides a ready-to-use implementation of time-series cross-validation. | Simplifies the process of creating multiple temporally valid train-test splits. [27] |
Statsmodels (ARIMA) |
Python Library | Offers a comprehensive suite for estimating and forecasting statistical models. | Used within each fold of a cross-validation loop to build and test time-series models. [27] |
| Sentinel-1/-2 & Copernicus DEM | Satellite Data | Provides multi-modal, multi-temporal satellite imagery and elevation data. | The foundational data for environmental time-series studies (e.g., landslides, LAI). Requires strict temporal splitting. [25] |
| High-Resolution Mass Spectrometry (HRMS) | Analytical Instrument | Generates complex, high-dimensional data for non-target analysis of contaminants. | Produces time-series data where machine learning models for source identification must avoid temporal leakage. [29] |
| Sen12Landslides Dataset | Benchmark Dataset | A curated dataset with pre- and post-event landslide imagery. | Serves as a benchmark for testing and validating spatio-temporal models with built-in temporal annotations. [25] |
Visualizing Model Architecture for Temporal Data
Advanced model architectures are being developed to better handle the challenges of long time-series forecasting. The following diagram illustrates the conceptual structure of a Temporal Mix of Experts (TMOE) model, which is designed to dynamically select relevant historical context and mitigate the influence of anomalous segments—a common issue in environmental sensor data [30].
In the realm of machine learning for environmental contaminant research, data preprocessing forms the foundational step that can determine the ultimate success or failure of predictive models. Data leakage during preprocessing represents a critical yet frequently overlooked threat that compromises model integrity, particularly in scientific applications such as groundwater pollution mapping and contamination classification. This phenomenon occurs when information from outside the training dataset—typically from the test set or future data—is used during model training, creating an overly optimistic performance assessment that fails to generalize in real-world scenarios [1]. In environmental research, where models inform public health decisions and resource allocation, such leakage can lead to inaccurate contamination risk assessments with significant societal consequences [31].
The insidious nature of preprocessing leakage lies in its ability to create models that appear highly accurate during validation yet perform poorly when deployed. A 2021 study analyzing scientific papers across 17 fields found that at least 294 publications were affected by data leakage, leading to overly optimistic performance metrics [1]. Within environmental contaminant research, this issue is particularly acute due to the complex, multivariate, and often sparse nature of contamination datasets [31]. As machine learning becomes increasingly integral to environmental science, establishing rigorous preprocessing protocols that prevent information leakage is paramount for generating reliable, actionable insights.
Understanding Preprocessing-Induced Data Leakage
Mechanisms of Leakage in Normalization and Feature Selection
Normalization leakage occurs when scaling parameters are calculated using the entire dataset before splitting into training and test sets. This common error allows the model to gain information about the global distribution of features, including those in the test set, which would not be available during actual deployment [32] [1]. For example, when predicting groundwater contaminant levels, applying min-max normalization across all samples before splitting can artificially inflate performance by allowing the model to "see" the range of values in the test set during training [33]. The proper approach involves calculating normalization parameters (e.g., mean, standard deviation, min, max) exclusively from the training data, then applying these same parameters to transform the test data [1].
Feature selection leakage represents another critical vulnerability, occurring when feature importance is evaluated using the entire dataset rather than only training data. This practice inadvertently reveals relationships between features and the target variable that exist in the test set, creating features that are artificially optimized for the specific dataset rather than generalizable patterns [33]. In contamination research, where identifying relevant environmental predictors is scientifically meaningful, this leakage can lead to incorrect conclusions about which factors truly influence contaminant transport and distribution [31]. For instance, when using recursive feature elimination or correlation-based selection, the evaluation must be performed solely on training data to prevent the model from learning test-specific patterns [33].
Impact on Environmental Research Models
The consequences of preprocessing leakage in environmental contaminant research extend beyond mere statistical inaccuracies to affect real-world decision-making. A recent study on groundwater contamination revealed that machine learning models compromised by data leakage could dramatically underestimate the prevalence of co-occurring pollutants, incorrectly suggesting that up to 80% of sampling locations had no contaminants above regulatory limits, while properly validated models indicated only 15-55% of locations were contamination-free [31]. Such discrepancies directly impact remediation prioritization and public health protection efforts.
Leakage during preprocessing typically produces several characteristic warning signs: unrealistically high performance metrics on validation data, significant performance degradation when models are deployed on new data, and discrepancies between validation performance and real-world utility [34] [1]. In one case study involving contamination classification of high-voltage insulators, researchers noted that proper attention to preprocessing protocols and leakage prevention was instrumental in achieving consistently high accuracy exceeding 98% across multiple machine learning models [12].
Table 1: Impact of Data Leakage on Model Performance in Environmental Applications
| Model Aspect | With Data Leakage | Without Data Leakage | Impact on Environmental Decisions |
|---|---|---|---|
| Reported Accuracy | Inflated by 15-25% [1] | Reflects true performance | Prevents overconfidence in contamination predictions |
| Generalization to New Locations | Poor performance on new geographic areas [31] | Maintains consistent performance | Enables reliable expansion to unmonitored sites |
| Feature Importance | Identifies spurious correlations | Reveals causally relevant factors | Correctly identifies true contaminant sources |
| Regulatory Compliance Predictions | Underestimates contamination extent [31] | Accurate risk assessment | Proper prioritization of remediation resources |
Methodologies for Leakage-Free Preprocessing
Strategic Data Splitting Protocols
Chronological splitting represents a fundamental strategy for temporal environmental data, such as contaminant concentration measurements collected over time. This approach ensures that models are trained on past data and validated on future observations, directly simulating the real-world prediction scenario [1]. For spatial contamination data, grouped splitting techniques prevent leakage by ensuring that all samples from the same geographic location or sampling campaign reside in either training or test sets, avoiding artificial inflation of performance through spatial autocorrelation [35].
Advanced computational tools now offer sophisticated solutions for leakage-free data partitioning. The DataSAIL framework, specifically designed for biological and environmental data, formulates optimal data splitting as a combinatorial optimization problem that minimizes similarity between training and test sets while preserving class distributions [35]. This approach is particularly valuable for contamination studies with limited sample sizes, where random splitting frequently results in highly similar molecules or environmental profiles appearing in both training and test sets. The DataSAIL algorithm employs clustering and integer linear programming to create splits where test samples demonstrate controlled dissimilarity from training instances, more accurately representing true out-of-distribution performance [35].
Pipeline-Based Preprocessing Implementation
Implementing preprocessing operations within a scikit-learn Pipeline provides a technical safeguard against normalization and feature selection leakage by automatically ensuring that all transformations are fitted exclusively on training data [33]. This approach encapsulates the entire sequence of preprocessing and modeling steps, guaranteeing that when the pipeline is applied to test data, the same training-derived parameters are used without information leakage from the test set.
The nested cross-validation approach provides an additional layer of protection against subtle leakage, particularly during hyperparameter tuning and model selection [1]. This methodology maintains multiple layers of data separation, with inner loops dedicated to parameter optimization and outer loops reserved for final performance estimation. For environmental contamination datasets with complex clusterings (e.g., samples from the same watershed, related chemical structures), grouped cross-validation ensures that all correlated samples remain within the same split, preventing the model from artificially learning cluster-specific patterns that wouldn't generalize to new contexts [35].
Domain-Specific Feature Engineering
In contamination research, temporal feature engineering requires particular vigilance to prevent leakage. Features such as rolling averages or seasonal decompositions must be computed using only historical data available at the time of prediction [1]. Similarly, when incorporating external datasets (e.g., land use records, weather data, industrial activity reports), researchers must ensure that these sources reflect information available prior to the prediction period rather than future data that wouldn't be accessible in operational scenarios [34].
Causal validation of features represents another critical leakage prevention strategy, wherein domain experts assess whether proposed features would genuinely be available and causally relevant at the time of prediction [1]. For instance, when predicting groundwater contamination, using features derived from water treatment outcomes that haven't yet occurred would constitute target leakage, as these represent future information unavailable during actual monitoring.
Preprocessing Workflow with Leakage Prevention
Experimental Validation in Contamination Research
Case Study: Groundwater Contaminant Prediction
A recent study funded by the NIEHS Superfund Research Program provides a compelling validation of leakage-free preprocessing methodologies for groundwater contamination prediction [31]. Researchers faced significant data challenges, with historical water quality databases containing sparse, inconsistent measurements of co-occurring pollutants across different locations and time periods. The research team implemented multiple imputation algorithms (AMELIA and MICE) to address missing data, carefully applying these methods within cross-validation folds to prevent information leakage from influencing the final performance estimates.
The experimental protocol involved rigorous data partitioning by geographical location and temporal sampling period, ensuring that models were evaluated on truly independent contamination scenarios. This approach revealed that standard random splitting had dramatically overestimated model performance, with leakage-free validation showing contamination at 45-85% of sampling locations compared to the 20% suggested by contaminated preprocessing [31]. The study further demonstrated that proper preprocessing enabled accurate identification of co-occurring pollutant patterns, essential for designing effective remediation strategies that address contaminant mixtures rather than individual chemicals.
Table 2: Experimental Results Comparison: With vs. Without Leakage Prevention
| Evaluation Metric | Standard Preprocessing (With Leakage) | Leakage-Free Preprocessing | Significance for Environmental Management |
|---|---|---|---|
| Predicted Clean Locations | 80% of sampling sites | 15-55% of sampling sites | More accurate risk assessment and targeting |
| Co-occurring Contaminant Detection | Limited identification | Comprehensive pattern recognition | Enables mixture toxicity assessment |
| Spatial Generalization | Poor performance on new regions | Maintained accuracy across regions | Reliable expansion to unmonitored areas |
| Statistical Significance | p < 0.05-0.10 | p < 0.05 | Robust findings for regulatory decisions |
Case Study: High-Voltage Insulator Contamination Classification
Research on contamination classification of high-voltage porcelain insulators further demonstrates the critical importance of leakage prevention in environmental monitoring applications [12]. The experimental design incorporated multiple safeguards against preprocessing leakage, including temporal splitting of leakage current measurements and grouped feature extraction where all features derived from a single insulator specimen remained within the same data split. The preprocessing workflow involved extracting critical features from time, frequency, and time-frequency domains of leakage current signals, with all feature selection procedures performed exclusively within training folds.
The implementation of these leakage prevention measures enabled the research team to develop models with exceptionally high accuracy (exceeding 98%) that maintained reliability across varying environmental conditions of temperature and humidity [12]. Notably, the study found that simpler models like decision trees, when properly preprocessing using leakage-free protocols, achieved comparable accuracy to complex neural networks but with significantly faster training times and optimization requirements. This finding has practical implications for deploying contamination monitoring systems in resource-constrained environmental settings.
Table 3: Research Reagent Solutions for Leakage-Free Preprocessing
| Tool/Category | Specific Examples | Function in Leakage Prevention |
|---|---|---|
| Data Splitting Frameworks | DataSAIL [35], scikit-learn StratifiedSplit | Minimizes similarity between training and test sets |
| Preprocessing Pipelines | scikit-learn Pipeline [33], MLflow | Encapsulates transformations to prevent test information leakage |
| Feature Selection Tools | Scikit-learn SelectKBest, Feature-engine [33] | Performs feature evaluation exclusively on training data |
| Validation Frameworks | Grouped Cross-Validation, TimeSeriesSplit [1] | Maintains proper data separation during model evaluation |
| Imputation Algorithms | AMELIA, MICE [31] | Handles missing data without leaking information |
| Monitoring & Detection | Model performance drift detection, feature correlation analysis [34] | Identifies potential leakage during model development |
Data Leakage Detection Protocol
In environmental contaminant research, where predictive models directly influence public health decisions and resource allocation, preventing data leakage during normalization and feature selection is not merely a technical consideration but an ethical imperative. The methodologies outlined in this guide—including strategic data splitting, pipeline-based preprocessing implementation, and domain-aware feature engineering—provide researchers with practical frameworks for maintaining model integrity. As machine learning applications in environmental science continue to expand, embracing these leakage prevention protocols will be essential for generating reliable, actionable insights that effectively address contamination challenges and protect vulnerable ecosystems and communities.
The rapid proliferation of synthetic chemicals has led to widespread environmental pollution from diverse sources including industrial effluents, agricultural runoff, and household products [29]. Effective contamination management hinges on precise source identification, which presents substantial analytical challenges. Traditional targeted chemical analysis methods are inherently limited to detecting predefined compounds, overlooking many known "unknowns" such as transformation products and emerging contaminants [29].
High-resolution mass spectrometry (HRMS)-based non-targeted analysis (NTA) has emerged as a powerful approach for detecting thousands of chemicals without prior knowledge [29] [36]. However, the principal challenge now lies not in detection itself, but in extracting meaningful environmental intelligence from the vast chemical datasets generated by HRMS-based NTA [29]. Machine learning (ML) offers transformative potential for this task, with algorithms capable of identifying latent patterns in high-dimensional data that traditional statistical methods often miss [29].
This case study examines the integration of ML with NTA for contaminant source identification, with particular emphasis on data leakage challenges that can compromise model reliability and lead to overstated performance metrics. We present a systematic framework for ML-assisted NTA, detailed experimental protocols, and critical considerations for ensuring robust implementation in environmental research.
Theoretical Foundation: ML-NTA Integration Framework
Core Concepts and Definitions
Non-Targeted Analysis (NTA) represents a discovery-based approach that uses HRMS to detect both known and unknown chemicals without predefinition [36] [37]. Unlike targeted methods that look for small, predefined chemical sets, NTA covers a much larger chemical space, enabling identification of previously unknown or understudied compounds [36].
Machine Learning in NTA involves applying computational algorithms to identify patterns in complex HRMS data that correlate with contamination sources. ML classifiers such as Random Forest, Support Vector Machines, and deep neural networks have demonstrated balanced accuracy ranging from 85.5% to 99.5% in distinguishing contamination sources based on chemical fingerprints [29].
Data Leakage occurs when information from outside the training dataset is used to create the model, resulting in overly optimistic performance estimates that fail to generalize to new data [38]. In environmental applications, this often manifests through spatial or temporal autocorrelation, where samples from the same location or time period are split across training and testing sets [38].
The ML-NTA Workflow Integration
The integration of ML and NTA for contaminant source identification follows a systematic four-stage workflow [29]:
- Sample Treatment and Extraction: Optimization of preparation techniques to balance selectivity and sensitivity while maximizing compound recovery.
- Data Generation and Acquisition: Utilization of HRMS platforms to generate complex datasets with detailed chemical information.
- ML-Oriented Data Processing and Analysis: Application of specialized computational methods to transform raw data into interpretable patterns.
- Result Validation: Implementation of multi-tiered validation strategies to ensure analytical and environmental relevance.
The Data Leakage Challenge in Environmental ML
Data leakage presents a particularly insidious challenge in ML-assisted NTA because it can produce models that appear highly accurate during development but fail completely in real-world applications. A critical case study in digital soil mapping demonstrated that conventional leave-sample-out cross-validation generated accuracy metrics 29-62% higher than more rigorous leave-profile-out cross-validation when vertical autocorrelation was present [38]. This inflation effect was even more pronounced with augmented datasets [38].
In NTA applications, similar risks emerge when chemical features from the same contamination event or sampling location are distributed across training and test sets, allowing models to effectively "memorize" source-specific signatures rather than learning generalizable patterns. This compromises the model's utility for policymaking and creates false confidence in its predictive capabilities [38].
Experimental Design and Methodologies
Sample Collection and Preparation Protocols
Sample Treatment and Extraction requires careful optimization to balance selectivity and sensitivity. Researchers must achieve a compromise between removing interfering components and preserving as many compounds as possible with adequate sensitivity [29].
- Purification Techniques: Solid phase extraction (SPE) is widely employed for its ability to enrich specific compound classes, though its inherent selectivity limits broad-spectrum coverage [29]. To address this limitation, multi-sorbent strategies combining Oasis HLB with ISOLUTE ENV+, Strata WAX, and WCX can achieve broader-range extractions [29].
- Extraction Methods: Green extraction techniques like QuEChERS, microwave-assisted extraction (MAE), and supercritical fluid extraction (SFE) improve efficiency by reducing solvent usage and processing time, particularly beneficial for large-scale environmental sampling campaigns [29].
Table 1: Key Research Reagent Solutions for NTA Sample Preparation
| Reagent/Category | Primary Function | Application Notes |
|---|---|---|
| Multi-sorbent SPE (Oasis HLB, ISOLUTE ENV+, Strata WAX/WCX) | Broad-spectrum analyte enrichment | Increases coverage of compounds with diverse physicochemical properties [29] |
| QuEChERS | Efficient extraction with minimal solvent use | Particularly suitable for large sample sets; reduces processing time [29] |
| Quality Control Samples | Monitoring analytical performance & batch effects | Essential for data quality assurance in ML workflows [29] |
| Certified Reference Materials (CRMs) | Compound identity verification & method validation | Critical for establishing analytical confidence in identifications [29] |
Data Generation via High-Resolution Mass Spectrometry
HRMS platforms, including quadrupole time-of-flight (Q-TOF) and Orbitrap systems, generate the complex datasets essential for NTA [29]. When coupled with liquid or gas chromatography (LC/GC), these instruments resolve isotopic patterns, fragmentation signatures, and structural features necessary for compound annotation [37].
Post-acquisition processing involves multiple computational steps [29]:
- Centroiding: Converting raw profile data to centroid data
- Peak Detection and Alignment: Identifying chromatographic peaks and aligning them across samples
- Componentization: Grouping related spectral features (adducts, isotopes) into molecular entities
The final output is a structured feature-intensity matrix, where rows represent samples and columns correspond to aligned chemical features, serving as the foundational dataset for ML-driven analysis [29].
ML-Oriented Data Processing and Analysis
The transition from raw HRMS data to interpretable patterns involves sequential computational steps designed specifically for ML applications [29]:
Data Preprocessing addresses fundamental data quality issues:
- Missing Value Imputation: Techniques like k-nearest neighbors (KNN) estimate plausible values for missing data points
- Normalization: Total ion current (TIC) normalization or similar approaches mitigate batch effects and analytical variance
- Data Alignment: Retention time correction, mass-to-charge ratio (m/z) recalibration, and peak matching ensure comparability across samples and batches [29]
Exploratory Analysis and Feature Selection identifies chemically meaningful patterns:
- Univariate Statistics: t-tests and Analysis of Variance (ANOVA) prioritize compounds with large fold changes between source categories
- Dimensionality Reduction: Principal component analysis (PCA) and t-distributed stochastic neighbor embedding (t-SNE) simplify high-dimensional data visualization [29]
- Feature Selection Algorithms: Recursive feature elimination optimizes input variables for model accuracy and interpretability
ML-NTA Workflow for Source Identification
Machine Learning Approaches and Implementation
Algorithm Selection and Performance
Multiple ML algorithms have demonstrated effectiveness for NTA applications, with selection dependent on specific research goals, data characteristics, and interpretability requirements [29].
Table 2: Machine Learning Algorithms for NTA Applications
| Algorithm | Best Suited Applications | Key Advantages | Reported Performance |
|---|---|---|---|
| Random Forest (RF) | Feature importance ranking, classification tasks | Handles high-dimensional data well, provides feature importance metrics [29] | Balanced accuracy: 85.5-99.5% (PFAS source classification) [29] |
| Support Vector Classifier (SVC) | Binary classification problems | Effective in high-dimensional spaces, robust to overfitting [29] | Balanced accuracy: 85.5-99.5% (PFAS source classification) [29] |
| Deep Belief Neural Network (DBNN) | Complex nonlinear relationships, noisy data | Strong generalization capabilities, robust to data noise [39] | R²: 0.982, RMSE: 3.77 (groundwater contamination) [39] |
| Automated ML (AutoML) | Rapid model development and deployment | Automates model selection and hyperparameter optimization [40] | Higher accuracy vs. XGBoost, RF, ETR, EN (groundwater case study) [40] |
| Partial Least Squares Discriminant Analysis (PLS-DA) | Identifying source-specific indicator compounds | Provides variable importance metrics, good interpretability [29] | Effective for identifying diagnostic chemical patterns [29] |
Advanced ML Applications in Environmental Contexts
Recent research has demonstrated the effectiveness of specialized ML approaches for specific environmental challenges:
Groundwater Contamination Source Identification (GCSI) presents particular challenges due to unknown boundary conditions and complex hydrogeological parameters. A novel AutoML approach has been developed as a surrogate for time-consuming simulation models, successfully identifying contaminant source information, model parameters, and boundary conditions simultaneously [40]. This AutoML surrogate demonstrated higher accuracy compared with XGBoost, Random Forest, Extra Trees Regressor, and ElasticNet methods [40].
Deep Learning Surrogates including Deep Belief Neural Networks (DBNN), Bidirectional Long Short-Term Memory Networks (BiLSTM), and Deep Residual Neural Networks (DRNN) have been employed to simulate highly non-linear relationships and establish direct mapping between simulation inputs and outputs [39]. In comparative studies, DBNN showed exceptional performance with R² values of 0.982, RMSE of 3.77, and MAE of 7.56%, demonstrating particular robustness to noise in monitoring data [39].
Critical Validation Strategies and Data Leakage Prevention
Tiered Validation Framework
Validation ensures the reliability of ML-NTA outputs through a comprehensive three-tiered approach [29]:
- Analytical Confidence Verification: Using certified reference materials (CRMs) or spectral library matches to confirm compound identities [29].
- Model Generalizability Assessment: Validating classifiers on independent external datasets, complemented by rigorous cross-validation techniques [29].
- Environmental Plausibility Checks: Correlating model predictions with contextual data, such as geospatial proximity to emission sources or known source-specific chemical markers [29].
Data Leakage Mitigation Protocols
Preventing data leakage requires careful experimental design and validation strategies:
Appropriate Cross-Validation Selection is critical for obtaining accurate performance estimates. For spatially or temporally correlated environmental data, leave-profile-out cross-validation (LPOCV) provides more realistic accuracy metrics than leave-sample-out cross-validation (LSOCV) [38]. In 3-dimensional digital soil mapping case studies, LSOCV generated overly optimistic accuracy metrics that were 29-62% higher than LPOCV for augmented datasets, and 8-18% higher for non-augmented data [38].
Temporal and Spatial Partitioning strategies ensure that samples collected from the same location or time period are not distributed across both training and testing sets. This prevents models from memorizing location-specific or time-specific signatures rather than learning generalizable chemical patterns.
Automated Machine Learning (AutoML) approaches can reduce human-induced bias in model selection and hyperparameter optimization, potentially mitigating some forms of data leakage [40]. However, careful implementation is still required to ensure proper data separation.
Data Leakage Prevention in ML-NTA
Applications and Case Studies
Chemical Space Characterization Across Environmental Media
The application of ML-NTA has revealed distinct chemical profiles across different environmental compartments, providing insights into source-specific contamination patterns [37].
Table 3: Characteristic Chemicals Identified by NTA Across Environmental Media
| Environmental Media | Frequently Detected Chemicals | Analytical Platform Prevalence | Source Implications |
|---|---|---|---|
| Water | Per- and polyfluoroalkyl substances (PFAS), pharmaceuticals [37] | LC-HRMS (51%), GC-HRMS (32%), Both (16%) [37] | Industrial discharges, wastewater treatment plants |
| Soil/Sediment | Pesticides, polyaromatic hydrocarbons (PAHs) [37] | LC-HRMS: ESI+ (18%), ESI- (22%), Both (43%) [37] | Agricultural runoff, historical contamination |
| Air | Volatile organic compounds (VOCs), semi-volatile organic compounds (SVOCs) [37] | GC-HRMS with EI (majority), CI (11%) [37] | Industrial emissions, combustion processes |
| Dust | Flame retardants, halogenated compounds [37] | LC-HRMS with ESI+ and/or ESI- [37] | Building materials, consumer products |
| Human Biospecimens | Plasticizers, pesticides, halogenated compounds [37] | LC-HRMS predominates [37] | Aggregate exposure across multiple pathways |
Groundwater Contamination Source Identification
Groundwater Contamination Source Identification (GCSI) represents a particularly challenging application area where ML-NTA has demonstrated significant value. Traditional GCSI approaches typically assumed boundary conditions as known variables, which often deviated from practical reality and led to distorted identification results [40] [39].
Advanced ML approaches have enabled simultaneous identification of contaminant source information, model parameters, and previously unknown boundary conditions [40]. Deep learning surrogate models, including Deep Belief Neural Networks (DBNN), have established direct mapping relationships between simulation model inputs and outputs, enabling rapid inverse identification based on actual monitoring data [39].
In robustness tests and cross-comparative ablation studies, DBNN showed exceptional performance with adaptability to GCSI research tasks, effectively handling uncertainty from noise in monitoring data [39].
Future Directions and Implementation Challenges
Current Limitations and Research Gaps
Despite significant advances, several challenges remain in the widespread implementation of ML-NTA for contaminant source identification:
Methodological Gaps include the absence of systematic frameworks bridging raw NTA data to environmentally actionable parameters [29]. Many existing reviews emphasize sample pretreatment and data acquisition while overlooking ML-oriented data processing pipelines capable of translating molecular features into source-relevant metrics.
Interpretability Challenges arise from the black-box nature of complex models like deep neural networks. While these models can achieve high classification accuracy, their limited transparency hinders the ability to provide chemically plausible attribution rationale required for regulatory actions [29].
Validation Deficiencies in current ML-assisted NTA studies remain fragmented and overly reliant on laboratory-based tests, potentially underperforming in real-world conditions involving field-validated source-receptor relationships [29].
Emerging Opportunities
Automated Machine Learning (AutoML) approaches show promise for streamlining model selection and hyperparameter optimization, reducing the human expertise required for effective implementation while maintaining high accuracy [40].
Deep Learning Advancements including Deep Belief Neural Networks (DBNN), Bidirectional Long Short-Term Memory Networks (BiLSTM), and Deep Residual Neural Networks (DRNN) offer increasingly sophisticated approaches for handling complex, non-linear relationships in environmental systems [39].
Standardization Initiatives led by organizations like the EPA aim to develop standardized methodologies for NTA, increasing accessibility and adoption across regulatory, academic, and commercial laboratories [36].
The integration of machine learning with non-target analysis represents a transformative approach for contaminant source identification, enabling researchers to extract meaningful environmental intelligence from complex chemical datasets. The systematic framework presented in this case study—encompassing sample treatment, data generation, ML-oriented processing, and rigorous validation—provides a roadmap for effective implementation.
The critical issue of data leakage must remain a central consideration throughout ML-NTA workflows, as inappropriate validation approaches can yield dramatically inflated performance metrics that fail to generalize to real-world applications. By adopting rigorous cross-validation strategies such as leave-profile-out approaches and maintaining clear separation between training and validation datasets, researchers can develop models with truly predictive capability.
As ML-NTA methodologies continue to mature, they offer unprecedented opportunities to identify previously unknown contamination sources, understand complex environmental transformations, and ultimately support more effective environmental protection measures. The ongoing development of standardized approaches, interpretable models, and robust validation frameworks will be essential for translating analytical capabilities into actionable environmental insights.
Leveraging Ensemble Models and Causal Frameworks for Mechanistic Insights Without Leakage
In the field of machine learning applied to environmental contaminant research, the pursuit of mechanistic insights—understanding the underlying causal processes—is paramount. However, this pursuit is often compromised by data leakage, a subtle but critical issue where information that should not be available during model training inadvertently influences the learning process, leading to overly optimistic performance metrics and models that fail in real-world applications [41] [7]. In artificial intelligence, data leakage refers to situations where information that should not be available at the time of prediction is inadvertently used during model training, undermining the model's ability to generalize to new data [41]. This problem is particularly acute in environmental science, where complex, heterogeneous datasets and the push for predictive modeling can overshadow the need for causally sound, interpretable insights [7].
This technical guide presents an integrated framework that combines ensemble modeling with causal inference methodologies to robustly discover mechanistic insights while rigorously preventing data leakage. Ensemble learning, which combines multiple models to achieve frameworks that perform as well as or better than the latest models, provides a powerful foundation for capturing complex, non-linear relationships in environmental data [42]. Meanwhile, modern causal frameworks move beyond correlation to uncover the underlying drivers and mechanisms governing environmental systems [43]. The integration of these approaches, governed by strict anti-leakage protocols, enables researchers to build models that are not only predictive but also interpretable and causally grounded.
Theoretical Foundations: Ensemble Learning and Causal Inference
Ensemble Learning Architectures
Ensemble learning mitigates the limitations of single models by combining multiple learners to improve overall accuracy, robustness, and generalizability. In environmental contexts, where data is often noisy and relationships complex, this diversity is particularly valuable [42] [44]. The core ensemble architectures include:
- Stacking (Stacked Generalization): Uses a meta-learner to optimally combine predictions from multiple base models (e.g., Naive Bayes, Random Forests, Gradient Boosting Machines). The stacking process leverages the strengths of each learner while mitigating their weaknesses, enabling enhanced predictive accuracy and robustness, particularly for complex, non-linear relationships [44].
- Hybrid Neural-Tree Ensembles: Combine deep neural layers (to capture complex, non-linear mappings and latent state representations) with tree-based ensembles (e.g., Extreme Gradient Boosted Trees, CatBoost) for robust handling of sparse, non-Gaussian feature distributions [45].
- Modular Framework Ensembles: Separate representation learning from effect estimation, using a reinforcement learning agent to dynamically adjust weights for each instance, balancing deep representations with statistical estimation [43].
Causal Inference Frameworks
Causal inference provides the theoretical foundation for moving beyond predictive patterns to understanding mechanistic relationships. Key frameworks include:
- Doubly Robust Estimation: Combines propensity score modeling and outcome regression to provide consistent effect estimates even if one of the models is misspecified, protecting against unobserved confounding [43].
- Causal Graph Discovery: Uses expert knowledge or algorithmic approaches (e.g., leveraging Shapley values for variable importance with cycle removal procedures) to generate valid causal directed acyclic graphs (DAGs) that formalize assumed causal relationships [43].
- Individualized Treatment Effect Estimation: Methods like X-Learner, Causal Forest, and Orthogonal Random Forest estimate how causal effects vary across subpopulations, crucial for understanding context-dependent mechanisms in heterogeneous environmental systems [43].
Data Leakage: Typology and Consequences
Data leakage manifests in several forms, each with distinct prevention strategies:
- Target Leakage: Occurs when training data includes features that are proxies for the target variable but would not be available at prediction time. For example, using a "payment status" column to predict loan default introduces future information [41].
- Train-Test Contamination: Happens when test data inadvertently influences the training process, often due to improper dataset splitting. In time-series data, this occurs when future observations leak into the training set, violating temporal ordering [41].
- Preprocessing Leakage: Arises when operations like normalization or imputation are applied to the full dataset before splitting, causing statistical information from test data to influence training [41].
Table 1: Data Leakage Types and Mitigation Strategies in Environmental Research
| Leakage Type | Definition | Common Causes in Environmental Research | Prevention Strategies |
|---|---|---|---|
| Target Leakage | Training data includes proxies for target variable | Using downstream effect measurements to predict upstream causes | rigorous causal graph development; temporal validation |
| Train-Test Contamination | Test data influences training process | Improper splitting of spatial or temporal data | spatial/temporal blocking; proper cross-validation |
| Preprocessing Leakage | Preprocessing uses global statistics | Normalizing entire dataset before splitting | Pipeline implementation; preprocessing fit only on training data |
| Feature Leakage | Engineered features use future information | Creating features using data from after prediction point | careful feature engineering; time-aware validation |
Integrated Methodological Framework
CAUSALRLSTACK Architecture for Environmental Applications
The CAUSALRLSTACK framework, adapted from healthcare applications, provides a modular approach that separates representation learning from causal effect estimation, making it particularly suitable for complex environmental data [43]. The architecture consists of four interconnected components:
- Causal Graph Construction: Two candidate causal graphs are constructed: one based on expert knowledge of environmental systems, and another discovered from data using computational methods that employ Shapley values to guide variable importance with cycle removal to generate valid causal DAGs. Sensitivity analysis selects the most suitable graph.
- Representation Learning Module: A memory-augmented Transformer captures complex, individualized representations from environmental data. The external memory allows the model to store and recall contextual information across samples, enhancing adaptability to distributional shifts common in environmental datasets.
- Causal Estimation Module: A doubly robust estimator (DRLearner) processes the representations to estimate causal effects, ensuring estimates remain consistent and less sensitive to bias even if either the outcome model or propensity model is misspecified.
- Reinforcement Learning-Based Ensemble: An RL agent dynamically adjusts weights between representation and estimation components for each instance, allowing the framework to adaptively balance deep representations with statistical estimation based on individual instance characteristics.
Ensemble Framework for Event Causality Identification
For environmental applications requiring identification of causal relationships between events (e.g., contaminant release → ecosystem response), an ensemble framework combining multiple architectural approaches proves effective [42]. This framework integrates:
- Mamba Architecture and Temporal Convolutional Networks (TCN): Capture long-range dependencies and temporal patterns in environmental time-series data.
- Graph Neural Networks (GNN): Model complex relational structures between environmental variables and events.
- k-Nearest Neighbor (kNN) Models: Provide instance-based predictions based on similarity to historical cases.
- Dual Graph Structures: Process all events from an environmental dataset within interconnected graph structures to increase local performance ability.
The ensemble employs weighted voting among base models, with fine-tuned DistilBERT serving as the foundation for text vectorization where textual data (e.g., scientific literature, monitoring reports) is involved [42].
Data Leakage Prevention Protocol
A rigorous, multi-layered protocol prevents data leakage throughout the analytical pipeline:
- Temporal Validation Splitting: For time-series environmental data, implement strict time-based splitting where training data always precedes validation data, which always precedes test data.
- Spatial Blocking: For spatially correlated environmental data, use spatial blocking to ensure nearby locations don't appear in both training and test sets.
- Pipeline-Integrated Preprocessing: All preprocessing (normalization, imputation, feature scaling) must be fit exclusively on training data, then applied to validation and test data without refitting.
- Causal Graph Validation: Verify that no features in the causal graph contain information that would not be available at prediction time, using domain expertise to identify potential target leakage.
- Comprehensive Feature Documentation: Maintain detailed documentation of all features, including their temporal availability and potential causal relationships with targets.
Table 2: Data Leakage Defense Checklist for Environmental ML Projects
| Phase | Checkpoint | Validation Method | Acceptance Criteria |
|---|---|---|---|
| Data Collection | Temporal Stamps | Verify all data points have accurate collection timestamps | No future information relative to prediction point |
| Feature Engineering | Causal Ordering | Review features against causal DAG | No downstream effects used to predict upstream causes |
| Data Splitting | Spatial/Temporal Structure | Visualize splits on map/timeline | No data leakage across splits; proper blocking used |
| Preprocessing | Pipeline Implementation | Check that preprocessing transformers fit only on training | No information from test set used in preprocessing |
| Model Training | Cross-Validation | Ensure nested CV for hyperparameter tuning | No hyperparameters optimized on test set |
| Evaluation | Baseline Comparison | Compare with simple, leakage-free models | Performance gains realistic and mechanistically explainable |
Experimental Implementation and Validation
Research Reagent Solutions for Environmental ML
Table 3: Essential Computational Tools for Ensemble Causal Modeling
| Tool/Category | Specific Examples | Function in Ensemble Causal Modeling |
|---|---|---|
| Statistical Software Packages | R, Python, SPSS, SAS, STATA | Provide foundational statistical operations, data management, and specialized causal inference packages [46]. |
| Machine Learning Libraries | Scikit-learn, XGBoost, CatBoost, H2O | Implement base learners (Random Forests, Gradient Boosting) and ensemble logic for stacking [44]. |
| Deep Learning Frameworks | PyTorch, TensorFlow, Keras | Enable implementation of neural components (Mamba, TCN, Transformers) for representation learning [42] [43]. |
| Causal Inference Packages | DoWhy, EconML, CausalML | Provide implementations of doubly robust estimators, meta-learners, and causal effect estimation methods [43]. |
| Data Visualization Tools | Matplotlib, Seaborn, Plotly, SHAP | Create model interpretability visualizations, causal graphs, and performance diagnostics [44]. |
| Workflow Management | MLflow, Kubeflow, Airflow | Orchestrate complex analytical pipelines while maintaining separation between training and test data [46]. |
Implementation Protocol: Stacked Ensemble for Contaminant Impact Assessment
The following step-by-step protocol details the implementation of a stacked ensemble model for assessing causal impacts of environmental contaminants, with explicit data leakage controls at each stage:
Phase 1: Data Preparation and Causal Graph Development
- Temporal Alignment: Align all environmental measurements with precise timestamps, ensuring cause precedes effect in temporal ordering.
- Causal Graph Construction: Develop initial causal DAG using both expert knowledge (environmental scientists) and data-driven discovery methods.
- Feature Engineering with Leakage Checks: Create features following the causal DAG, explicitly verifying no feature incorporates information from after the prediction point.
Phase 2: Base Model Training with Leakage Prevention
- Data Partitioning: Split data using temporal blocking, ensuring training period (e.g., 2005-2015), validation period (2016-2018), and test period (2019-2021) maintain strict temporal sequence.
- Base Learner Training: Train multiple diverse base models (Random Forest, Gradient Boosting, Temporal Convolutional Networks, etc.) on the training period only.
- Hyperparameter Optimization: Use nested temporal cross-validation exclusively within the training period to tune hyperparameters.
Phase 3: Stacked Ensemble Construction
- Meta-Feature Generation: Generate predictions from all base models on the validation period to create the meta-feature dataset.
- Meta-Learner Training: Train the meta-learner (e.g., XGBoost, Generalized Linear Model) on the meta-feature dataset to learn optimal combination of base model predictions [44].
- Causal Effect Integration: Apply doubly robust estimation to the ensemble predictions to derive final causal effect estimates, adjusting for potential confounding.
Phase 4: Validation and Leakage Testing
- Temporal Robustness Check: Validate model on multiple test periods to ensure consistent performance without temporal decay.
- Placebo Testing: Test model with placebo treatments (known non-causes) to verify it doesn't detect spurious relationships.
- Leakage Audit: Conduct comprehensive audit of the entire pipeline to confirm no information from test periods influenced training.
Performance Metrics and Validation Framework
Rigorous validation of ensemble causal models requires multiple performance dimensions:
- Predictive Accuracy: Standard metrics (Accuracy, AUC-ROC, F1-Score) evaluated on properly held-out test data [44].
- Causal Effect Calibration: Assessment of how well estimated treatment effects match ground truth (when available) or pass placebo tests.
- Robustness to Confounding: Evaluation of how sensitive results are to unmeasured confounding using sensitivity analysis.
- Generalization Across Contexts: Testing model performance across different spatial regions, time periods, or environmental conditions.
Table 4: Quantitative Performance Comparison of Ensemble Methods in Environmental Applications
| Model Architecture | Accuracy | AUC-ROC | F1-Score | Causal Effect MSE | Robustness to Confounding |
|---|---|---|---|---|---|
| Single Model (GBM) | 0.872 | 0.923 | 0.861 | 0.154 | Low |
| Simple Ensemble (Voting) | 0.891 | 0.945 | 0.882 | 0.132 | Medium |
| Stacked Ensemble (XGBoost Meta-Learner) | 0.939 | 0.994 | 0.931 | 0.098 | High [44] |
| Hybrid Neural-Tree Ensemble | 0.921 | 0.978 | 0.915 | 0.087 | High [45] |
| CAUSALRLSTACK Framework | 0.861 | 0.897 | 0.845 | 0.076 | Very High [43] |
The integration of ensemble modeling with causal inference frameworks represents a paradigm shift in environmental data science, moving beyond purely predictive approaches toward truly mechanistic understanding. The structured methodologies presented in this guide—particularly the CAUSALRLSTACK architecture and stacked ensemble implementation—provide researchers with robust tools to extract causally valid insights from complex environmental data while maintaining vigilance against data leakage.
Future advancements in this field will likely focus on several key areas: (1) development of more sophisticated temporal causal discovery methods that can automatically detect and adjust for potential leakage in time-series data; (2) integration of physical model components with ensemble learners to create hybrid models that respect known environmental mechanisms while learning from data; and (3) automated leakage detection systems that can scan analytical pipelines for potential contamination points. As noted in recent research, "complicated biological and ecological data and ensemble models revealing mechanisms and spatiotemporal trends with strong causal relationships and without data leakage deserve more attention" in environmental research [7].
By adopting the rigorous framework presented here, environmental researchers can ensure their machine learning models produce not just statistically significant results, but mechanistically meaningful insights that genuinely advance our understanding of environmental systems and support evidence-based decision-making.
Detecting and Diagnosing Leaks: A Troubleshooting Guide for ML Practitioners
In the field of machine learning (ML) applied to environmental contaminant research, the reliability of predictive models is paramount for informing regulatory decisions and remediation strategies. Data leakage represents a critical threat to this reliability, often leading to overoptimistic results and a reproducibility crisis in scientific findings [47]. A survey of literature across 17 scientific fields found that data leakage collectively affected 294 papers, underscoring the pervasive nature of this problem [1] [47]. In environmental contexts, such as forecasting chemical fate or predicting contamination sources, leakage can cause models to fail upon deployment, leading to misguided resource allocation and ineffective policy measures [16] [29].
This guide provides a detailed taxonomy focusing on three specific types of code-level data leakage—Overlap, Multi-Test, and Preprocessing Leakage. These categories are crucial for researchers, scientists, and drug development professionals working with high-dimensional data from sources like high-resolution mass spectrometry (HRMS) in non-targeted analysis (NTA) [29]. Understanding and mitigating these leakage types is the first step toward ensuring that ML models generate actionable and trustworthy environmental insights.
A Detailed Taxonomy of Leakage Types
Data leakage in machine learning occurs when information from outside the training dataset is inadvertently used to create the model, leading to performance estimates that do not generalize to real-world, unseen data [1] [48]. The following taxonomy, derived from analysis of ML code, categorizes three common leakage types [49].
Table 1: Core Types of Data Leakage in Machine Learning
| Leakage Type | Core Concept | Typical Phase of Occurrence | Primary Impact on Model |
|---|---|---|---|
| Overlap Leakage | Test data is directly used for training or hyperparameter tuning [49]. | Dataset Construction, Model Training | Severely inflated performance due to direct exposure to test samples. |
| Multi-Test Leakage | Test data is used repeatedly for evaluation and model tuning decisions [49]. | Model Evaluation, Hyperparameter Tuning | Overfitting to the specific test set, compromising generalizability. |
| Preprocessing Leakage | Test data is merged with training data for preprocessing operations [49]. | Data Preprocessing | Indirect information leak from test set, creating biased performance. |
Overlap Leakage
Overlap leakage, also known as leaky data splits, constitutes a fundamental error where the integrity of the train-test split is violated. This occurs when test data is directly used for training or for hyperparameter tuning [49]. In environmental research, a typical example involves the improper application of data augmentation techniques. For instance, using SMOTE (Synthetic Minority Over-sampling Technique) oversampling on the entire dataset before splitting it into training and testing sets would cause the model to be trained on synthetic data derived from the test set [49]. This gives the model an unfair preview of the data distribution it will be tested on, resulting in severely inflated performance metrics that crumble when the model is applied to genuinely new data from a different location or time period.
Multi-Test Leakage
Multi-test leakage arises from the improper repeated use of the test set during the model development lifecycle. This form of leakage occurs when the test set is used not just for a single, final evaluation, but repeatedly for tasks such as algorithm selection, model selection, and hyperparameter tuning [49]. A common scenario is performing hyperparameter tuning with GridSearchCV coupled with RepeatedKFold cross-validation on the entire dataset. This setup inadvertently bakes information from the test set into the model tuning process [49]. For environmental scientists, this is akin to continuously calibrating an instrument using the same validation sample—the model becomes highly specialized to that particular test set but fails to predict new, unseen contamination events, ultimately leading to poor generalization.
Preprocessing Leakage
Preprocessing leakage is a subtle but widespread issue where the test data influences the preprocessing steps that are fitted on the training data. This happens when operations such as normalization, scaling, imputation of missing values, or feature selection are applied to the entire dataset before it is split into training and testing sets [1] [49]. For example, if a MinMaxScaler is fit on the entire dataset (containing both training and test samples), the scaled training data will contain information about the distribution of the test set [49]. In environmental workflows, where tools like Principal Component Analysis (PCA) are used for dimensionality reduction of complex HRMS data, applying PCA before a train-test split is a critical error [29]. This allows the model to leverage global statistical properties that would not be available in a real-world prediction scenario, creating a biased and overly optimistic view of model performance.
Figure 1: Correct data splitting prevents preprocessing leakage. Preprocessing must be fitted on the training data only.
Quantitative Impact of Data Leakage in Scientific Research
The impact of data leakage extends beyond theoretical concern; it has tangible consequences for scientific validity and resource allocation. The table below synthesizes findings from surveys and case studies across multiple fields, illustrating the scope of the problem.
Table 2: Documented Impact of Data Leakage Across Research Fields
| Field of Study | Number of Papers Reviewed | Papers with Leakage Pitfalls | Common Leakage Types Identified |
|---|---|---|---|
| Medicine / Clinical Epidemiology | 71 | 48 | Feature selection on train and test set [50] |
| Radiology | 62 | 16 | No train-test split; duplicates in sets; sampling bias [50] |
| Neuropsychiatry | 100 | 53 | No train-test split; preprocessing on train and test sets together [50] |
| Law (ECHR) | 171 | 156 | Illegitimate features; temporal leakage; non-independence [50] |
| Various (17 fields) | Not Specified | 294 | Various, leading to overly optimistic conclusions [1] [47] |
The repercussions of these leaks are severe. A National Library of Medicine study found that data leakage can inflate or deflate performance metrics, compromising the models' utility for diagnosing illness or identifying treatments [1]. In a specific case study on civil war prediction, when data leakage errors were corrected, the supposed superiority of complex ML models disappeared, and they performed no better than decades-old logistic regression models [47] [50]. This translates directly into resource wastage, as finding and fixing leakage after a model is trained requires retraining from scratch, which is computationally expensive and time-consuming [1].
Detection and Prevention Methodologies
Experimental Protocols for Leakage Detection
Implementing rigorous experimental protocols is essential for identifying and preventing data leakage. The following methodologies, drawn from software and research best practices, can be integrated into the ML pipeline for environmental data.
Code-Level Analysis with Cross-Validation: Manually review code or use automated tools to check for errors like preprocessing before splitting [49]. Employ time-series cross-validation for temporal environmental data (e.g., chemical concentration over time). This method ensures that the model is always trained on past data and tested on future data, preventing temporal leakage [1]. A key red flag is inconsistent cross-validation results where some folds show much higher performance than others [48].
Feature Importance and Ablation Analysis: Use model interpretability techniques to examine the features your model relies on most heavily. If features that are not logically available at the time of prediction (e.g., future values, global aggregates) show high importance, it is a strong indicator of target leakage [1] [48]. Conduct a sensitivity analysis by systematically removing suspicious features and observing the change in model performance on a held-out validation set; a significant performance drop may point to leakage [48].
Hold-Out Set Validation: The most robust method is to use a strict hold-out validation set that is completely untouched during the entire model development process, including exploratory data analysis, feature engineering, and hyperparameter tuning [1] [49]. This set, representative of real-world data, provides the final, unbiased estimate of model performance. A significant drop in performance between the test set and this hold-out set is a clear sign that leakage has occurred during development.
Figure 2: A leakage-resistant validation protocol using a hold-out set.
A Proactive Framework for Leakage Prevention
Prevention is the most effective strategy against data leakage. This involves establishing a robust and systematic framework for handling data.
Implement Pipelines for Preprocessing: Instead of applying preprocessing steps individually, use ML pipelines (e.g.,
sklearn.pipeline.Pipeline) that bundle all preprocessing and modeling steps together. This ensures that when cross-validation is performed, transformers like scalers and imputers are fitted only on the training folds of each split, and then applied to the validation fold, preventing preprocessing leakage [1].Adopt Model Info Sheets: Inspired by work on the reproducibility crisis, using a "model info sheet" is a practical tool for self-assessment [47] [50]. This checklist requires researchers to explicitly document and justify key decisions, including how data was split, how preprocessing was handled, and the legitimacy of all features used. This practice enforces accountability and makes potential leakage sources visible.
Temporal Splitting for Environmental Data: Given that environmental data (e.g., seasonal contamination levels, multi-year monitoring) is often time-dependent, a simple random train-test split is inappropriate. Always split data chronologically, using a fixed point in time [1] [48]. All data before the cutoff is used for training, and all data after for testing. This mimics the real-world prediction scenario and is the most effective way to prevent temporal leakage.
The following table details essential software tools and practices crucial for implementing the detection and prevention methodologies outlined in this guide.
Table 3: Essential Tools and Practices for Leakage Prevention
| Tool / Practice | Category | Primary Function in Leakage Prevention |
|---|---|---|
| Scikit-learn Pipeline | Software Tool | Bundles preprocessing and modeling to ensure correct fitting/transforming during cross-validation [1]. |
| TimeSeriesSplit | Software Tool | A cross-validator for time-series data that prevents future data from leaking into the training set [1]. |
| Automated Code Analysis | Software Tool | Scans ML codebases to identify patterns associated with common data leakage errors [49]. |
| Strict Hold-Out Set | Best Practice | Provides an unbiased estimate of model performance on unseen data, serving as a final leakage check [1] [49]. |
| Model Info Sheets | Best Practice | A documentation framework that forces explicit justification for data splitting, features, and preprocessing [47] [50]. |
| Domain Expert Review | Best Practice | Scrutinizes features and model behavior to identify unrealistic or unavailable data used in predictions [1]. |
In the high-stakes field of environmental contaminant research, where model predictions can directly influence public health policy and multi-million-dollar remediation projects, the integrity of machine learning models is non-negotiable. Overlap, Multi-Test, and Preprocessing Leakage represent critical vulnerabilities that can compromise this integrity, leading to a reproducibility crisis and a loss of trust in data-driven science [47] [50]. By adopting the detailed taxonomy, rigorous detection protocols, and proactive prevention framework outlined in this guide, researchers can fortify their workflows against these insidious errors. A commitment to methodological rigor, supported by the tools and practices in the "Scientist's Toolkit," is the foundation for building ML models that are not only powerful but also reliable and actionable in protecting our environment.
Exploratory Data Analysis and Model Inspection for Leaky Feature Detection
Data leakage represents a critical failure mode in machine learning (ML) for environmental contaminant research, occurring when information unavailable during real-world prediction time is used during model training [1]. This phenomenon creates models with overly optimistic performance during validation that fail catastrophically when deployed for genuine prediction tasks, such as forecasting contaminant spread or estimating toxicological effects [1] [49]. In environmental research, where models inform public health decisions and regulatory policies, leakage-induced failures can lead to severe consequences including resource misallocation, inaccurate risk assessments, and eroded scientific credibility [1].
The fundamental mechanism of leakage involves the illicit transfer of information between training and evaluation phases, creating models that recognize patterns specific to the test set rather than learning generalizable relationships [49]. A National Library of Medicine study found that across 17 different scientific fields, at least 294 published papers were affected by data leakage, suggesting this problem permeates scientific research [1]. In environmental contaminant research specifically, leakage often manifests through temporal contamination, where future observations influence historical models, or through proxy variables that indirectly encode the target variable [41].
Types and Mechanisms of Data Leakage
Classification of Leakage Pathways
Data leakage in ML follows distinct pathways that can be categorized based on their mechanism of occurrence. Understanding these categories enables more systematic detection and prevention strategies [1] [49].
Table 1: Types and Mechanisms of Data Leakage in Machine Learning
| Leakage Type | Mechanism | Environmental Research Example | Primary Detection Method |
|---|---|---|---|
| Target Leakage | Inclusion of features that would not be available at prediction time [1] | Using future contaminant measurements to predict current exposure levels | Feature availability timeline analysis |
| Train-Test Contamination | Improper splitting or preprocessing that allows information exchange between training and test sets [1] | Applying normalization to entire dataset before temporal splitting | Pipeline integrity verification |
| Preprocessing Leakage | Performing data transformations before train-test split [49] | Imputing missing soil contamination values using statistics from full dataset | Preprocessing sequence audit |
| Temporal Leakage | Using future data to predict past events without chronological separation [1] | Training on mixed chronological water quality data to predict historical contamination | Time-series validation |
| Multi-Test Leakage | Repeated use of test data for model selection and evaluation [49] | Using same test set for hyperparameter tuning and final evaluation | Validation protocol review |
Domain-Specific Leakage Scenarios in Environmental Research
Environmental contaminant research presents unique leakage challenges due to its complex temporal dynamics, spatial dependencies, and measurement constraints. For instance, using laboratory-analyzed contaminant concentrations to predict field-sensor measurements creates target leakage when the laboratory results become available after field deployment [1]. Similarly, spatial leakage occurs when training and test sets contain samples from adjacent geographical areas with correlated contamination levels, violating the assumption of independent observations [41].
Another common scenario involves proxy variable leakage, where seemingly legitimate features indirectly encode the target variable. For example, using "regulatory action status" to predict contaminant levels creates leakage if such actions are typically initiated after contamination is confirmed [1]. Similarly, features derived from advanced instrumentation may incorporate calibration information that won't be available during field deployment of screening models.
Methodologies for Leaky Feature Detection
Exploratory Data Analysis for Leakage Identification
Exploratory Data Analysis (EDA) provides powerful techniques for identifying potential leakage before model training. These methods focus on pattern recognition, distribution analysis, and relationship mapping to detect anomalous data relationships suggestive of leakage [1].
Temporal EDA Protocols:
- Chronological Splitting Validation: Split data by time stamps before analysis, ensuring EDA only examines training temporal segments [1]
- Feature-Target Timeline Mapping: For each feature, document when it becomes available relative to target measurement in real-world scenarios
- Rolling Window Correlation: Calculate moving correlations between features and target to identify periods where relationships violate causal timing
- Lag Analysis: Systematically test associations between target variable and lagged/forward features to detect temporal leakage
Distributional EDA Protocols:
- Train-Test Distribution Comparison: Apply statistical tests (Kolmogorov-Smirnov, Jensen-Shannon divergence) to compare feature distributions between training and test sets after proper splitting
- Feature-Target Association Strength: Calculate mutual information and correlation metrics between each feature and target; unusually high values may indicate leakage [1]
- Clustering-Based Anomaly Detection: Apply unsupervised clustering to identify samples with anomalous feature-target relationships
Table 2: Statistical Tests for Leaky Feature Detection in EDA
| Test Method | Application Context | Leakage Indicator | Implementation Protocol |
|---|---|---|---|
| Difference in Distribution Tests | Comparing train/test feature distributions | Significant p-values (<0.01) suggest improper splitting | Apply Kolmogorov-Smirnov or Chi-square tests after proper data partitioning |
| Mutual Information Analysis | Measuring feature-target dependency | Exceptionally high values suggest potential target leakage | Calculate normalized mutual information; values >0.5 warrant investigation |
| Permutation Feature Importance | Assessing feature contribution to model | Features with disproportionate importance may be leaky | Train model on actual data vs. permuted data; compare importance scores |
| Temporal Autocorrelation | Time-series data analysis | Significant autocorrelation across split boundary indicates temporal leakage | Calculate autocorrelation function at split point |
Model Inspection Techniques
Model inspection provides complementary approaches to EDA for identifying leakage through analysis of trained models and their behavior [1].
Feature Importance Analysis Protocol:
- Train multiple model types (random forest, gradient boosting, logistic regression) using identical preprocessing
- Calculate feature importance scores using permutation importance, SHAP values, and model-specific importance metrics
- Identify features with consistently high importance across all model types
- Subject high-importance features to domain expert review for logical availability at prediction time [1]
Performance Discrepancy Testing Protocol:
- Train models and evaluate performance on proper validation sets
- Create artificial leakage by introducing known leaky features (e.g., slight target derivatives)
- Compare performance metrics between original and leakage-augmented models
- Models showing significant performance improvement with artificial leakage may already contain leaky features
Cross-Validation Anomaly Detection Protocol:
- Implement stratified time-series cross-validation appropriate for environmental data [1]
- Monitor performance metrics across folds; unusually low variance may indicate leakage [1]
- Calculate feature importance stability across folds; highly stable importance patterns may indicate leakage
- Compare cross-validation performance with truly held-out temporal validation sets
Experimental Workflow for Comprehensive Leakage Detection
The following experimental workflow integrates EDA and model inspection techniques into a systematic leakage detection pipeline suitable for environmental contaminant research.
Workflow Implementation Protocol
The leakage detection workflow implements a systematic approach to identifying and eliminating data leakage through sequential testing and validation stages. Implementation requires strict adherence to temporal partitioning throughout all analysis stages [1].
Phase 1: Data Preparation and Partitioning
- Documentary Audit: Create complete feature provenance documentation including measurement methods, timing, and processing history
- Temporal Splitting: Split data chronologically at the outset, preserving the most recent period for final validation [1]
- Feature Freezing: Finalize feature set before any analysis to prevent data-driven feature selection bias
Phase 2: Iterative Leakage Screening
- Automated Distribution Testing: Apply statistical tests between training and validation feature distributions
- Domain Logic Validation: Subject feature-target relationships to expert review for temporal plausibility
- Model-Based Detection: Train multiple model types and identify consistently high-importance features for scrutiny
Phase 3: Validation and Iteration
- Temporal Performance Comparison: Compare cross-validation performance with true temporal validation
- Leakage Scoring: Calculate integrated leakage probability score combining multiple detection methods
- Feature Set Refinement: Remove or transform suspect features and retrain models iteratively
Research Reagent Solutions for Leakage Detection
Implementing effective leakage detection requires both methodological rigor and appropriate computational tools. The following table catalogues essential "research reagents" for constructing a comprehensive leakage detection pipeline.
Table 3: Essential Research Reagent Solutions for Data Leakage Detection
| Tool Category | Specific Solution | Function in Leakage Detection | Implementation Considerations |
|---|---|---|---|
| Data Partitioning | TimeSeriesSplit (Scikit-learn) | Creates temporal splits that respect chronological order | Requires careful handling of seasonal patterns in environmental data |
| Statistical Testing | Scipy Stats (K-S tests, correlation analysis) | Quantifies distributional differences between datasets | Multiple testing correction needed when screening many features |
| Feature Importance | SHAP, Permutation Importance | Identifies features with disproportionate model influence | Computational intensity scales with dataset size and model complexity |
| Visualization | Matplotlib, Seaborn, Plotly | Creates distribution plots and temporal trend visualizations | Accessibility requirements mandate colorblind-friendly palettes [51] |
| Pipeline Management | Scikit-learn Pipelines, MLflow | Ensures proper preprocessing sequence and experiment tracking | Critical for maintaining separation between training and test processing |
| Automated Detection | Active Learning Approaches [49] | Applies machine learning to identify leakage patterns in code | Requires annotated dataset of leakage examples for training [49] |
Implementation Protocols for Research Reagents
Temporal Partitioning Protocol:
- Import TimeSeriesSplit from sklearn.model_selection
- Define maximum training size and test size based on environmental data frequency
- Implement forward chaining validation to simulate real-world model updates
- Preserve most recent 20% of temporal data for final hold-out validation
Feature Importance Calculation Protocol:
- Compute permutation importance using sklearn.inspection.permutation_importance
- Calculate SHAP values using appropriate explainer for model type
- Generate model-specific importance scores (Gini importance for random forests)
- Aggregate importance scores across multiple validation folds
- Normalize importance scores to range [0,1] for cross-feature comparison
Automated Leakage Detection Protocol:
- Implement active learning framework for leakage detection [49]
- Initialize with small set of labeled leakage examples
- Iteratively select most informative samples for expert labeling
- Retrain detection model on expanded labeled set
- Continue until detection performance stabilizes across multiple environmental datasets
Validation Framework and Performance Metrics
Validating leakage detection effectiveness requires specialized metrics that capture the unique challenges of identifying illicit information transfer in environmental data.
Leakage Detection Metrics
Temporal Performance Decay Measurement:
- Calculate performance difference between cross-validation and temporal hold-out validation
- Compute decay ratio: (CVperformance - Holdoutperformance) / CV_performance
- Establish threshold values for leakage suspicion based on domain-specific requirements
Feature Importance Stability Metric:
- Calculate coefficient of variation for feature importance across validation folds
- Low variation suggests consistent feature importance potentially indicating leakage
- Compare stability patterns between known valid features and suspected leaky features
Integrated Leakage Score:
- Combine multiple indicators: temporal decay, importance stability, domain logic violation
- Apply weighted scoring based on environmental context and consequence severity
- Establish threshold values for required feature review or elimination
Environmental Research Validation Protocol
For environmental contaminant research, validation requires domain-specific adaptations to account for spatial and temporal autocorrelation common in environmental data.
Spatio-Temporal Validation Protocol:
- Implement spatial blocking during cross-validation to prevent geographical leakage
- Combine temporal splits with spatial clustering for comprehensive validation
- Measure performance separately for different geographical regions to identify location-specific leakage
- Validate across multiple temporal scales (seasonal, annual, decadal) relevant to environmental processes
Domain Expert Integration Protocol:
- Establish feature review committee with environmental science expertise
- Develop standardized feature evaluation rubric assessing temporal plausibility
- Implement blinded review process for feature availability assessment
- Document rationale for feature inclusion/exclusion decisions
This comprehensive framework for leaky feature detection through exploratory data analysis and model inspection provides environmental researchers with systematic methodologies for identifying and eliminating data leakage, thereby enhancing the reliability and real-world applicability of predictive models for contaminant research.
This technical guide examines the convergence of automated code analysis and machine learning (ML) for detecting data leakage and contamination in critical research environments. For pharmaceutical development and environmental science researchers, these technologies provide essential safeguards for protecting sensitive data and ensuring research integrity. The integration of Static Application Security Testing (SAST) tools with specialized ML algorithms creates a multi-layered defense system against both digital data leaks and physical research contamination. This whitepaper presents quantitative comparisons of leading solutions, detailed experimental protocols for leakage detection systems, and visual workflows to guide implementation for research professionals operating in data-intensive environments.
Automated Code Analysis: Foundation for Secure Research Environments
Automated code analysis tools systematically scan source code to identify vulnerabilities, errors, and quality issues before applications are deployed in research environments [52]. These tools function as essential infrastructure for preventing data leakage in pharmaceutical and environmental research systems where sensitive patient data, experimental results, and proprietary methodologies must be protected.
Core Mechanisms and Classification
Code analysis tools operate through three primary methodologies [52]:
- Static Analysis (SAST): Examines code at rest without executing the application, detecting vulnerabilities and insecure patterns early in development.
- Dynamic Analysis: Tests running applications to uncover runtime flaws such as input validation errors.
- Hybrid Approaches: Combine static and dynamic methods within modern DevSecOps workflows.
For research institutions handling sensitive environmental or patient data, these automated checks reduce risk, improve efficiency, and form a core building block of application security [52].
Quantitative Analysis of Leading Code Analysis Tools
The table below summarizes the capabilities of prominent code analysis tools evaluated for research environments:
Table 1: Comparative Analysis of Code Security Tools for Research Applications
| Tool Name | Primary Focus | Key Strengths | Research Environment Suitability |
|---|---|---|---|
| Cycode | AI-native platform unifying AST, SCA, and ASPM | Code-to-cloud traceability to eliminate alert noise [52] | High - Comprehensive coverage for diverse research codebases |
| Snyk Code | Developer-first scanning | Fast, real-time SAST focused on developer workflows [52] | Medium - Ideal for agile research teams |
| Semgrep | Customizable rule-based analysis | Lightweight, flexible SAST allowing custom rules [52] | High - Adaptable to specialized research needs |
| Aikido Security | AI-powered SAST and code quality | Low false positives (<10%), predictable pricing [53] | High - Cost-effective for academic budgets |
| SonarQube | Code quality and maintenance | Combines basic SAST with technical debt checks [52] | Medium - Good for established research codebases |
| Veracode | Compliance and governance | Policy-driven analysis for regulatory compliance [52] | High - Essential for clinical research data |
These tools address the critical challenge that 73% of security leaders acknowledge: "code is everywhere," while 63% report that CISOs aren't investing sufficiently in code security [52]. For research organizations, this investment gap creates significant vulnerability in protecting sensitive experimental data and preventing leaks.
Machine Learning for Leakage and Contamination Detection
Machine learning approaches provide sophisticated capabilities for detecting both digital data leaks and physical contamination in research environments, with applications ranging from source code analysis to high-voltage insulator monitoring in experimental settings.
ML-Enhanced Code Analysis for Data Leak Prevention
Advanced code analysis platforms now incorporate machine learning to improve detection accuracy and reduce false positives. Advanced platforms like Aikido Security use AI-driven static code analysis that learns from team coding patterns, tailoring reviews to specific standards and significantly reducing noise from false positives [53]. This capability is particularly valuable in research environments where development patterns may be highly specialized.
According to industry data, nearly 70% of organizations have discovered vulnerabilities in AI-generated code, with 1 in 5 of these incidents escalating into serious breaches [53]. This underscores the critical importance of ML-enhanced analysis tools in modern research infrastructures that increasingly incorporate AI-generated code components.
Experimental Protocol: ML for Contamination Classification
Research demonstrates the application of machine learning for contamination detection in physical research environments, particularly relevant for environmental contaminant studies. The following experimental protocol outlines a methodology validated for classifying contamination levels in high-voltage insulators using leakage current analysis [12], providing a template for similar contamination detection applications:
Table 2: Research Reagent Solutions for Contamination Detection Experiments
| Reagent/Material | Specification | Experimental Function |
|---|---|---|
| Porcelain Insulators | Standard high-voltage type | Primary test subject for contamination accumulation |
| Leakage Current Sensor | Precision measurement capability | Captures current flow across contaminated surfaces |
| Environmental Chamber | Controlled T/H conditions | Simulates real-world environmental conditions |
| Data Acquisition System | Multi-channel, high-frequency | Records leakage current parameters over time |
| Pollution Constituents | Dust, salt, industrial particles | Creates standardized contamination mixtures |
Experimental Methodology [12]:
Sample Preparation: Artificially pollute porcelain insulators divided into three contamination classes (high, moderate, low) using standardized pollution constituents.
Data Collection: Develop a comprehensive dataset of leakage current for porcelain insulators with varying pollution levels under controlled laboratory conditions, including critical parameters of temperature and varying humidity to reflect environmental impacts.
Feature Extraction: Preprocess the generated dataset and extract critical features from time, frequency, and time-frequency domains to characterize leakage current patterns.
Model Training: Train and evaluate four distinct machine learning models, including decision trees and neural networks, using Bayesian optimization for parameter tuning.
The experimental results demonstrated exceptional performance, with accuracies consistently exceeding 98% [12]. Notably, decision tree-based models exhibited significantly faster training and optimization times compared to neural network counterparts, suggesting practical implementation advantages for research environments with computational constraints.
Integrated Framework for Research Data Protection
A comprehensive data protection strategy for research environments requires integrating automated code analysis with ML-powered leakage detection, creating a multi-layered defense system appropriate for pharmaceutical development and environmental research applications.
Implementation Framework
The diagram below illustrates the integrated framework for research data protection combining automated code analysis with ML-powered leakage detection:
Quantitative Performance Metrics
Implementation of these integrated systems yields measurable improvements in research data protection:
Table 3: Performance Metrics for ML-Enhanced Security Systems
| Metric Category | Baseline (Traditional Tools) | ML-Enhanced Performance | Impact on Research Integrity |
|---|---|---|---|
| Vulnerability Detection Accuracy | 70-85% | 95-98% [12] | Prevents data corruption in research datasets |
| False Positive Rate | 15-30% | <10% [53] | Reduces researcher alert fatigue |
| Mean Time to Remediation | 7-14 days | 1-2 days [52] | Accelerates research project timelines |
| Contamination Classification Accuracy | Manual: 85-90% | Automated: >98% [12] | Improves experimental reliability |
For pharmaceutical research organizations, these metrics translate to direct benefits in protecting patient data and maintaining regulatory compliance. According to industry reports, organizations using security AI and automation save an average of $1.9 million per breach and shorten the breach lifecycle by 80 days [53].
Implementation Guidelines for Research Organizations
Successful deployment of automated code analysis and ML-powered leakage detection systems requires strategic planning aligned with research workflows and compliance requirements.
Integration with Research Environments
Research organizations should prioritize tools that offer:
- Developer-Friendly Integrations: Native support for GitHub, GitLab, Bitbucket, and CI/CD pipelines used in research software development [53].
- Customizable Rule Sets: Adaptability to specialized research codebases and unique data types.
- Compliance Support: Automated alignment with regulatory frameworks including HIPAA, SOC 2, PCI DSS, and NIH data security requirements [53].
- Predictable Pricing: Cost structures compatible with research grant funding cycles.
Future Directions
Emerging trends indicate continued convergence of code analysis and machine learning technologies, with particular relevance for research environments:
- AI-Powered Autofix: Automated remediation of detected vulnerabilities, reducing manual effort and accelerating research deployment cycles [53].
- Cross-Domain ML Models: Adaptation of contamination detection algorithms from physical systems to digital data leakage scenarios.
- Federated Learning: Privacy-preserving model training across multiple research institutions without sharing sensitive data.
For research professionals in pharmaceutical development and environmental science, these advanced solutions provide critical infrastructure for maintaining data integrity, protecting sensitive information, and ensuring the reliability of research outcomes in increasingly complex digital and physical environments.
Best Practices for Pipeline Architecture and Cross-Validation in Environmental Datasets
This guide details best practices for constructing robust data pipelines and implementing rigorous cross-validation for machine learning (ML) applications in environmental science. With the global data pipeline tools market projected to grow from $6.8 billion in 2021 to $35.6 billion by 2031, mastering these disciplines is critical for research reliability [54]. Data leakage—where information from the test set inappropriately influences model training—poses a severe threat to scientific validity, affecting hundreds of studies across multiple fields and leading to overoptimistic results that fail in real-world deployment [47]. This technical brief provides actionable frameworks for pipeline architecture and validation strategies specifically designed to address these challenges in environmental contaminant research.
Foundations of Data Pipeline Architecture for Environmental Research
A data pipeline is the foundational process for moving and transforming data from source systems to analytical destinations. In environmental research, this typically involves extracting data from diverse sources like field sensors, satellite imagery, and laboratory databases; cleaning and transforming it; and loading it into target systems like data warehouses for analysis [54] [55]. A well-architected pipeline ensures data integrity, accessibility, and security while significantly reducing manual workloads for researchers and data scientists [54].
Modern data pipelines have evolved from simple one-way transport mechanisms into dynamic, bidirectional systems that power everything from business dashboards to personalized user experiences. This evolution has been driven by the rise of cloud-native tools, streaming platforms, and the explosion of data sources [55]. The separation of storage and compute introduced by platforms like Snowflake, and the shift from ETL (Extract, Transform, Load) to ELT (Extract, Load, Transform) represent key innovations that provide data teams with the flexibility to store everything and process only what's needed [55].
Critical Pipeline Architecture Patterns
Environmental research projects must select architecture patterns aligned with their specific data characteristics and analytical requirements. The table below summarizes common patterns used across modern scientific data stacks.
Table 1: Data Pipeline Architecture Patterns for Environmental Research
| Pattern | Description | Best For Environmental Applications | Key Considerations |
|---|---|---|---|
| ETL (Extract, Transform, Load) | Data is extracted from sources, transformed outside the warehouse, then loaded into a destination [55]. | Smaller environmental datasets; transformations too complex for warehouse execution. | Adds pipeline complexity but preserves warehouse compute resources. |
| ELT (Extract, Load, Transform) | Raw data is loaded directly into the warehouse first, then transformed in-place using SQL or tools like dbt [55]. | Most modern environmental research stacks; preserves raw data for reprocessing. | Becomes default for cloud-native stacks; simplifies ingestion pipelines. |
| Streaming-First Pipelines | Data is streamed via tools like Kafka and processed incrementally for low-latency applications [55]. | Real-time environmental monitoring, early warning systems for contaminants. | Prioritizes speed over completeness; often complements batch pipelines. |
| Reverse ETL | Modeled data is synced from analytical warehouses back into operational tools and field systems [55]. | Deploying predictive models to field equipment or monitoring networks. | Powers real-time personalization and operational triggers. |
Implementing Robust Cross-Validation for Spatial Environmental Data
Standard random cross-validation fails dramatically with spatial environmental data due to spatial autocorrelation—the principle that nearby locations tend to have similar environmental characteristics [56]. This autocorrelation violates the fundamental assumption of independence between training and test sets, leading to overoptimistic performance estimates and models that fail to generalize to new locations [57] [56].
Spatial cross-validation addresses this by separating data based on geographical proximity. However, implementing effective spatial cross-validation requires careful methodological choices. Research on marine remote sensing applications has demonstrated that block size is the most critical parameter, while block shape, number of folds, and assignment to folds have minor effects on error estimates [56]. The optimal blocking strategy should reflect the data structure and application context, such as leaving out whole hydrological subbasins for testing in watershed studies [56].
Advanced Cross-Validation Methods for Environmental Data
The table below compares specialized cross-validation methods developed to address unique challenges in environmental datasets.
Table 2: Cross-Validation Methods for Environmental Data Challenges
| Method | Core Approach | Environmental Application Context | Performance Advantages |
|---|---|---|---|
| Spatial Block CV | Splits data into geographical blocks for testing [56]. | Spatially clustered samples (e.g., monitoring stations, field plots). | Prevents overoptimism from spatial autocorrelation. |
| Dissimilarity-Adaptive CV (DA-CV) | Categorizes prediction locations as "similar/different" based on covariate dissimilarity in feature space; applies random CV to "similar" and spatial CV to "different" groups [57]. | Datasets with varying degrees of spatial clustering; generalized transferability assessment. | Provides accurate evaluations in 85% of scenarios with clustered samples [57]. |
| K-fold with Bayesian Optimization | Combines K-fold validation with Bayesian hyperparameter optimization for enhanced parameter tuning [58]. | Complex model optimization with limited environmental data (e.g., remote sensing classification). | Improved ResNet18 classification accuracy by 2.14% on EuroSat dataset [58]. |
| Integrated CV & Bootstrapping | Applies both cross-validation and bootstrapping techniques to strengthen model validation [59]. | Small environmental datasets with high variance; groundwater quality assessment. | RF-CV model achieved R²=0.87 vs. RF-B R²=0.80 in groundwater quality prediction [59]. |
Preventing Data Leakage in Environmental Machine Learning
Data leakage represents a critical threat to the validity of ML-based environmental research. It occurs when information from the test set inadvertently influences the training process, leading to inflated performance metrics that don't generalize to new data [47] [49]. A systematic survey found leakage affects at least 294 papers across 17 scientific fields, contributing to what some term a "reproducibility crisis" in machine-learning-based science [47].
In one illustrative case study from civil war prediction, when data leakage errors were corrected, complex ML models showed no substantive performance advantage over decades-old logistic regression models [47]. This pattern likely extends to environmental applications, where leakage can create false confidence in predictive models for contaminant transport or ecological risk assessment.
Data Leakage Taxonomy and Detection Strategies
Researchers should be vigilant for these common leakage types [49]:
- Overlap Leakage: Occurs when test data is directly used for training or hyperparameter tuning, such as when augmentation methods (e.g., SMOTE oversampling) are incorrectly applied before data splitting [49].
- Multi-test Leakage: Happens when test data is used repeatedly for evaluation and decision-making (algorithm selection, model selection, hyperparameter tuning) instead of using separate validation data [49].
- Pre-processing Leakage: Arises when test data is merged with training data for pre-processing operations like feature selection, normalization, or PCA projection [49].
Automated detection approaches using transfer learning, active learning, and low-shot prompting have shown promise for identifying leakage in ML code, with active learning achieving an F-2 score of 0.72 while reducing needed annotated samples from 1,523 to 698 [49].
Integrated Experimental Protocol for Environmental ML
This section provides a detailed methodology for implementing robust pipeline architecture and cross-validation in environmental contaminant research, drawing from validated approaches in recent literature.
Data Pipeline Implementation Protocol
Phase 1: Modular Pipeline Design Adopt a data product mindset, treating your pipeline as a reusable analytical asset rather than a one-off tool [54]. Implement a modular, cloud-native architecture that separates ingestion, storage, transformation, and consumption layers [60] [55]. For environmental data, specifically include:
- Specialized connectors for environmental data sources (sensor networks, satellite imagery APIs, laboratory information management systems)
- Temporal alignment modules for time-series data from multiple sources
- Geospatial validation components to verify coordinate integrity and projection consistency
Phase 2: Data Integrity Assurance Implement comprehensive validation checks at every pipeline stage, from data ingestion to transformation and loading [54]. Leverage automated data profiling tools such as Great Expectations to define and test data quality expectations [54]. For contaminant research, include:
- Range validation for physicochemical parameters based on environmental plausibility
- Consistency checks between related parameters (e.g., pH and metal solubility)
- Automated anomaly detection for sensor malfunction or field sampling errors
Phase 3: Governance and Monitoring Establish a rigid data governance framework ensuring transparency and accountability [54]. Implement automated monitoring systems that track pipeline performance and provide feedback on bottlenecks and anomalies [54]. Utilize platforms with built-in monitoring capabilities like Grafana for continuous pipeline evaluation [54].
Spatial Cross-Validation Implementation Protocol
Phase 1: Experimental Design Assessment
- Characterize the spatial structure of your environmental data using correlograms of predictors to inform block size selection [56]
- Quantify spatial autocorrelation using Moran's I or similar indices
- Identify natural spatial units (watershed boundaries, geological formations, airsheds) for ecologically meaningful blocking
Phase 2: DA-CV Implementation For datasets with varying spatial clustering, implement Dissimilarity-Adaptive Cross-Validation:
- Calculate dissimilarity between prediction locations and sampled locations using feature space distance metrics
- Categorize locations into "similar" and "different" groups based on dissimilarity thresholds
- Apply random CV to "similar" locations and spatial CV to "different" locations
- Compute final evaluation metrics through weighted averaging of both groups [57]
Phase 3: Model Selection and Validation
- Apply spatial block CV with block sizes informed by Phase 1 analysis
- Combine with Bayesian hyperparameter optimization for enhanced parameter tuning [58]
- Validate selected models on completely held-out spatial regions or time periods not used in any optimization stage
Diagram 1: Integrated environmental data pipeline and validation architecture showing the interconnection between robust data engineering and spatial validation methodologies.
The Scientist's Toolkit: Essential Research Reagents
Table 3: Essential Computational Reagents for Environmental ML Research
| Tool/Category | Function | Representative Examples | Application Notes |
|---|---|---|---|
| Data Pipeline Orchestration | Author, schedule, and monitor workflows programmatically [55] [61]. | Apache Airflow, AWS Glue, Prefect | Airflow offers high customization but requires significant setup [61]. |
| Spatial Cross-Validation | Implement spatial separation schemes for model validation [57] [56]. | R package 'blockCV', DA-CV method, kNNDM | blockSize parameter should be informed by correlogram analysis [56]. |
| Cloud Data Warehouses | Scalable storage and compute for large environmental datasets [54] [55]. | Snowflake, Google BigQuery, Amazon Redshift | Enable separation of storage and compute; support ELT patterns [55]. |
| Data Transformation | Transform data within analytical environments using SQL [54] [55]. | dbt (data build tool), Dataform | Implements version-controlled, modular transformation logic [55]. |
| Hyperparameter Optimization | Find optimal model parameters through systematic search [58]. | Bayesian Optimization, Grid Search, Random Search | Combined with K-fold CV for enhanced accuracy [58]. |
| Leakage Detection | Identify potential data leakage in ML code automatically [49]. | Active Learning approaches, Transfer Learning | Active learning reduces needed annotated samples by 54% [49]. |
Diagram 2: Cross-validation methodology comparison illustrating the progression from problematic random approaches to sophisticated adaptive methods that address spatial dependency challenges.
Robust data pipeline architecture and rigorous, spatially-aware cross-validation are not merely technical implementation details but fundamental requirements for producing valid, reliable machine learning applications in environmental contaminant research. By adopting the modular pipeline frameworks and adaptive validation methodologies outlined in this guide, researchers can significantly reduce data leakage risks and build models that generalize successfully to new environmental contexts. The integrated approach presented here—combining engineering best practices with spatially explicit validation strategies—provides a comprehensive framework for addressing the unique challenges posed by environmental datasets and moving toward more reproducible environmental data science.
Ensuring Real-World Performance: Validation and Comparative Analysis of ML Models
The integration of machine learning (ML) into environmental contaminant research promises a revolution in prediction accuracy and operational efficiency. However, a critical vulnerability threatens this potential: data leakage, where models perform well on pristine laboratory data but fail in real-world conditions. This whitepaper examines the root causes of this issue, notably the mismatch between controlled lab data and complex environmental realities. We present evidence that field-validated, large-scale frameworks are not merely beneficial but essential for developing robust, trustworthy ML models that can genuinely support environmental science and regulatory decision-making.
Machine learning is reshaping environmental research, offering powerful tools for predicting chemical hazards, monitoring pollution, and assessing risks. In traditional laboratory settings, ML models frequently demonstrate exceptional performance, with reported accuracies often exceeding 95% in controlled studies [12]. However, this high performance often masks a significant problem: models trained exclusively on laboratory data tend to fail when confronted with the complexity of real-world environmental systems [7]. This phenomenon, a form of data leakage, occurs when the training data does not adequately represent the deployment environment, leading to overly optimistic performance estimates and models that are unreliable for practical applications.
The core of the issue lies in the fundamental disparities between laboratory and field conditions. Lab data, while valuable for establishing baseline mechanisms, often lacks the matrix effects, trace concentrations, and complex scenarios encountered in natural ecosystems [7]. Furthermore, the scarcity of high-quality, large-scale field data creates a bottleneck that forces researchers to rely on limited datasets, increasing the risk of models that overfit and underperform [17]. Moving beyond this limitation requires a paradigm shift towards integrated research frameworks that prioritize field validation and large-scale data collection from the outset.
The Laboratory-Field Disconnect: Quantifying the Gap
The disconnect between laboratory studies and environmental reality manifests in several critical areas, each contributing to the potential for data leakage in ML models.
Critical Omissions in Laboratory Data
Laboratory datasets often lack the multi-dimensional features that characterize real-world environments. The following table summarizes key disparities that can lead to model failure if not addressed.
Table 1: Key Disparities Between Laboratory and Field Data Leading to Data Leakage
| Feature Dimension | Typical Laboratory Data | Essential Field Data | Risk of Omission |
|---|---|---|---|
| Environmental Parameters | Controlled, constant temperature/humidity | Dynamic, fluctuating conditions [12] | Model fails under varying real-world climates |
| Pollutant Matrix | Single contaminant in purified medium | Complex mixtures (e.g., microplastics, antibiotics, PFAS) [7] | Inaccurate prediction of interaction effects |
| Spatiotemporal Trends | Limited time points, single location | Long-term, geographically distributed trends [7] | Inability to forecast large-scale environmental impacts |
| Concentration Levels | High, standardized concentrations | Trace, fluctuating concentrations [7] | Poor sensitivity for actual environmental detection |
The Data Scarcity Bottleneck
The reliance on lab data is exacerbated by a significant scarcity of field data. A bibliometric analysis of ML in environmental chemical research, encompassing 3,150 publications, reveals an exponential growth in model development since 2015 [16]. However, this analysis also highlights a critical bias: the field is dominated by environmental science journals, with a 4:1 research bias toward environmental endpoints over human health endpoints [16]. This indicates that even when field data is used, it may not be integrated with the complex biological and ecological data necessary for a holistic risk assessment, creating another form of data leakage where models are blind to crucial health implications.
Case Study: Experimental Protocol for Field-Validated ML
The following case study exemplifies a rigorous methodology for developing a contamination classification model with a minimized risk of data leakage, using field-informed laboratory data.
Experimental Design and Dataset Development
A study on classifying pollution levels of high-voltage porcelain insulators demonstrates a robust approach to creating a realistic dataset [12]. The experimental protocol was designed to bridge the lab-field gap:
- Objective: To classify insulator contamination into High, Moderate, and Low levels using leakage current signals.
- Dataset Generation: A meticulous dataset of leakage current was developed under controlled laboratory conditions. Crucially, critical parameters of temperature and varying humidity were included to reflect the impact of environmental conditions and bring the dataset closer to real-world scenarios [12].
- Pollution Classes: Artificially polluted insulators were prepared to represent three distinct contamination classes, ensuring labeled data for supervised learning.
Feature Extraction and Model Training
The generated dataset was processed to extract features that capture real-world signal characteristics, a critical step for generalizable model performance.
- Multi-Domain Feature Extraction: To capture comprehensive signal patterns, features were extracted from three domains:
- Time Domain: Analyzing the raw signal over time.
- Frequency Domain: Transforming the signal to identify frequency components.
- Time-Frequency Domain: Using methods like wavelet transforms to capture non-stationary signal features [12].
- Model Training and Optimization: Four distinct ML models, including decision trees and neural networks, were trained. The Bayesian optimization technique was used to optimize the models' hyperparameters, ensuring they were finely tuned to the dataset [12].
Results and Validation
The models demonstrated exceptional performance, with accuracies consistently exceeding 98% on the validated dataset [12]. Notably, the study provided a key insight for resource allocation: decision tree-based models exhibited significantly faster training and optimization times compared to neural network counterparts, making them highly efficient for such applications [12]. This end-to-end workflow, from realistic data generation to model validation, provides a template for building more reliable ML systems.
The following diagram illustrates the integrated experimental workflow, highlighting steps that mitigate data leakage risk.
A Framework for Integrated Environmental Assessment
To systematically address data leakage, researchers must adopt holistic frameworks that are designed for integration from the outset. Such frameworks consider the entire lifecycle of a substance and multiple data sources.
The Footprint and Handprint Framework
A proposed holistic framework for pharmaceuticals offers a valuable model for integrated sustainability assessment [62]. Its core components are highly applicable to environmental ML:
- Lifecycle Stages: The framework mandates assessment across all stages, from development and production to use and disposal, forcing data collection beyond isolated lab studies [62].
- Three Pillars of Sustainability: It evaluates environment, social, and economic impacts, ensuring ML models are trained on data that reflects multi-faceted real-world constraints and objectives [62].
- Footprint and Handprint: It considers both the burdens (
footprint) and the societal benefits (handprint) of a substance, preventing narrow optimization that could lead to unintended consequences [62].
Adopting such a framework ensures that data collection and model development are guided by a comprehensive understanding of the problem space, reducing the risk of building models that are accurate only within a limited, artificial context.
Overcoming Data Collection Barriers
Implementing these frameworks requires confronting the significant challenges of environmental data collection. These challenges, if not managed, directly introduce data leakage by creating biased training sets.
Table 2: Key Challenges in Environmental Data Collection and Mitigation Strategies
| Challenge Category | Specific Issues | Potential Mitigation Strategies |
|---|---|---|
| Technical & Logistical | Sensor calibration drift, equipment failure in harsh conditions, accessing remote sites [63] | Use of robust sensor networks, routine QA/QC protocols, hybrid data from satellites and mobile sensors |
| Data Integration | Disparate formats, units, and quality from sources like satellites, sensors, and citizen science [63] | Development of data harmonization standards and automated data cleaning pipelines |
| Socio-Political & Economic | High costs, limited funding, political influence, strategic underreporting, lack of global standards [63] | Fostering international collaboration, open data initiatives, and transparent data governance models |
The Scientist's Toolkit: Essential Research Reagents and Solutions
Building field-validated ML models requires a suite of "research reagents"—both data and computational tools. The following table details key solutions for constructing robust environmental ML pipelines.
Table 3: Research Reagent Solutions for Field-Validated ML
| Tool Category | Specific Examples | Function & Rationale |
|---|---|---|
| Data Generation & Collection | Artificially polluted physical samples (e.g., insulators [12]), Sensor networks (e.g., for PM2.5 [16]), Satellite imagery | Creates realistic training data that bridges the lab-field gap. Provides large-scale, spatial-temporal field data. |
| Feature Engineering | Time, Frequency, and Time-Frequency domain analysis [12] | Extracts robust, multi-domain features from raw signals (e.g., leakage current) that are informative under varying conditions. |
| ML Algorithms | Tree-Based Models (Random Forest, XGBoost [16]), Neural Networks, Bayesian Models [16] | Provides a suite of models for different needs; tree-based models often offer a good balance of performance and computational efficiency for environmental data [12]. |
| Model Optimization & Interpretation | Bayesian Optimization [12], SHapley Additive exPlanations (SHAP) [64] | Automates hyperparameter tuning for peak performance. Provides model interpretability, crucial for stakeholder trust and regulatory acceptance. |
| Data Fusion & Harmonization | Geospatial analysis tools, Data standardization protocols | Integrates disparate data sources (e.g., sensor readings, satellite data, social vulnerability indices [64]) into a cohesive dataset for modeling. |
The path forward for machine learning in environmental science requires a fundamental commitment to field validation and large-scale frameworks. The risks associated with data leakage from lab-confined models are too significant to ignore, potentially leading to flawed predictions and misguided policies. Future research must prioritize:
- Integrated Data Collection: Designing studies that incorporate field-level complexities—such as matrix effects, trace concentrations, and dynamic environmental parameters—from the very beginning.
- Explainable AI (XAI): Widely adopting techniques like SHAP to interpret model outcomes, build trust with stakeholders, and verify that predictions are based on environmentally sound reasoning [64].
- International Collaboration: Overcoming data scarcity and harmonizing data collection standards globally to build the comprehensive, high-quality datasets needed to power the next generation of environmental ML models [63].
By embracing these principles, the scientific community can move beyond the limitations of lab data and develop machine learning tools that are truly capable of understanding and predicting the complex dynamics of our natural environment.
In environmental contaminant research, machine learning (ML) models are increasingly deployed to replace or assist costly laboratory studies [7]. However, this field faces a significant challenge: data leakage that severely compromises model reliability [38]. Data leakage occurs when information from the testing dataset inadvertently influences the model training process, creating overly optimistic performance metrics that fail to generalize to real-world scenarios. This problem is particularly acute in environmental contexts where spatial or temporal autocorrelation exists, such as when soil samples from the same profile or water samples from the same monitoring station are split across training and test sets [38].
The consequences of improper model validation extend beyond academic concerns—they undermine the scientific foundation for environmental policy and risk assessment. Without rigorous validation, policymakers and stakeholders may use map products and predictive models with the false impression that they are more accurate than they truly are [38]. This paper introduces a comprehensive framework for tiered validation that integrates traditional reference materials with environmental plausibility checks to address these critical issues.
Core Concepts: Data Leakage and Validation Fundamentals
The Data Leakage Problem in Environmental Contexts
Data leakage represents a fundamental threat to ML model reliability in environmental science. It occurs when there is any overlap between data used for model fitting and hyperparameter tuning, and those used for testing [38]. This overlap creates biased performance metrics that do not reflect the model's true predictive capability on unseen data.
In 3-dimensional digital soil mapping (DSM), for example, conventional leave-sample-out cross-validation (LSOCV) results in contamination of the test dataset due to vertical autocorrelation of soil properties from different samples within the same profile [38]. Studies demonstrate that with augmented datasets, LSOCV generates accuracy metrics that are 29–62% higher than more appropriate validation approaches like leave-profile-out cross-validation (LPOCV) [38]. This inflation of performance highlights how traditional validation methods can fail dramatically in environmental contexts with inherent data dependencies.
Foundational Validation Techniques
Model validation serves as the critical process for testing how well a machine learning model performs with data it hasn't seen during training [65]. Several foundational techniques form the building blocks for more sophisticated tiered approaches:
- Hold-out Methods: The most basic approach splits data into training and testing sets, with variations including simple train-test splits and train-validation-test splits [65].
- Cross-Validation: K-fold cross-validation splits the dataset into k equal-sized folds, training the model on k-1 folds and testing on the remaining fold, repeating this process k times [66].
- Stratified Cross-Validation: Ensures each fold maintains the same class distribution as the full dataset, particularly valuable for imbalanced environmental data [66].
- Leave-One-Out Cross-Validation (LOOCV): Trains the model on all data points except one, which is used for testing, repeating for each data point in the dataset [66].
Table 1: Comparison of Fundamental Validation Techniques
| Technique | Best For | Advantages | Limitations |
|---|---|---|---|
| Train-Test Split | Large datasets, quick baselines | Simple, fast computation | High variance, sensitive to split |
| K-Fold CV | Small to medium datasets | Reduced bias, efficient data use | Computationally intensive |
| Stratified K-Fold | Imbalanced classification | Maintains class distribution | Added complexity |
| LOOCV | Very small datasets | Low bias, uses all data | High variance, computationally expensive |
Tiered Validation Framework: A Multi-Layered Approach
Conceptual Framework and Workflow
A robust tiered validation strategy integrates multiple validation layers to address different potential failure modes in ML models for environmental applications. The following diagram illustrates the comprehensive workflow for implementing this approach:
Tier 1: Technical Performance Validation
The first tier focuses on quantifying predictive performance using appropriate computational validation techniques that prevent data leakage:
Stratified K-Fold Cross-Validation for Imbalanced Data Environmental datasets often exhibit significant class imbalance, such as when contamination events are rare. Standard k-fold cross-validation can produce misleading performance metrics in these cases. Stratified k-fold CV ensures each fold preserves the same percentage of samples of each target class as the complete dataset [67]. For a dataset with 5% highly contaminated samples, each fold would maintain this 5% representation.
Leave-Profile-Out Cross-Validation for Spatial Data For 3-dimensional environmental data like soil profiles or water columns, leave-profile-out cross-validation (LPOCV) is essential. This method partitions all samples from the same profile entirely to either training or test sets, preventing data leakage from vertical autocorrelation [38]. Implementation requires careful data structuring to ensure complete profile segregation.
Time Series Split for Temporal Data Environmental data collected over time requires specialized validation approaches that respect temporal ordering. Time series split validation ensures that models are tested on future data points relative to their training data, preventing leakage from future to past [67]. This approach is particularly relevant for monitoring changing contamination patterns.
Table 2: Technical Validation Methods for Specific Data Structures
| Data Structure | Recommended Method | Key Implementation Consideration |
|---|---|---|
| Independent Samples | K-Fold Cross-Validation | Default for IID (independent and identically distributed) data |
| Imbalanced Classes | Stratified K-Fold CV | Preserves class distribution in each fold |
| Spatial/Temporal | LPOCV or Time Series Split | Maintains data integrity by avoiding autocorrelation leakage |
| Very Small Datasets | Leave-One-Out CV | Maximizes training data but computationally expensive |
Tier 2: Environmental Plausibility Checks
The second tier moves beyond statistical performance to assess whether model predictions align with established environmental principles and mechanisms.
Biological and Ecological Plausibility Assessment Biological plausibility consists of two principal aspects: a "generalizability aspect" concerning the validity of inferences from experimental models to real-world scenarios, and a "mechanistic aspect" concerning certainty in knowledge of biological mechanisms [68]. For environmental contaminants, this means evaluating whether predicted effects align with known toxicological pathways and exposure-response relationships.
Causal Relationship Analysis ML models in environmental science should reveal mechanisms and spatiotemporal trends with strong causal relationships [7]. This involves examining whether predicted patterns follow established cause-effect pathways, such as known biochemical transformation processes or physical transport mechanisms. For instance, a model predicting contaminant dispersion should respect fundamental hydrologic principles.
Matrix Influence and Complex Scenario Evaluation Environmental models must account for matrix effects—how the composition of environmental media (water, soil, air) influences contaminant behavior. Validation should include testing model performance across different environmental matrices and under complex real-world scenarios rather than relying solely on simplified laboratory conditions [7].
Tier 3: Experimental Validation with Reference Materials
The third tier establishes ground truth through experimental validation using certified reference materials and controlled studies.
Reference Materials as Benchmark Tools Certified reference materials (CRMs) with known contamination levels provide essential benchmarks for validating model predictions. These materials allow for direct comparison between predicted and actual contaminant concentrations, serving as an objective performance measure independent of training data.
Controlled Laboratory Validation Protocols A comprehensive experimental validation framework includes developing controlled datasets that reflect real-world variability. For example, in validating ML models for high-voltage insulator contamination classification, researchers created a meticulous dataset of leakage current for porcelain insulators with varying pollution levels under controlled laboratory conditions, including critical parameters of temperature and humidity [12]. This approach brings datasets closer to real-world scenarios while maintaining controlled conditions for validation.
Multi-Tiered Experimental Design Advanced validation employs a multi-tiered experimental approach, as demonstrated in drug repurposing research where machine learning predictions underwent large-scale retrospective clinical data analysis, standardized animal studies, molecular docking simulations, and dynamics analyses [69]. This hierarchical experimental validation provides converging evidence from complementary methodologies.
Implementation Guide: Protocols and Materials
Experimental Protocol for Leakage Current-Based Contamination Classification
The following protocol adapts methodologies from experimental ML validation in engineering to environmental contexts:
Sample Preparation
- Collect representative environmental samples (soil, water, biota) spanning expected contamination gradients
- Characterize samples using standard analytical methods to establish reference values
- Divide samples into training, validation, and testing sets using appropriate spatial/temporal partitioning
Feature Extraction and Preprocessing
- Preprocess raw sensor or analytical data to remove artifacts and noise
- Extract features from time, frequency, and time-frequency domains where applicable [12]
- Apply feature ranking algorithms to identify most predictive variables
- Normalize features to standard scales while preventing data leakage
Model Training with Bayesian Optimization
- Train multiple ML models (decision trees, neural networks, ensemble methods) using training set
- Employ Bayesian optimization for hyperparameter tuning [12]
- Validate technical performance using tiered cross-validation approaches
- Select optimal model based on balanced performance metrics
Experimental Validation
- Test model predictions against certified reference materials
- Conduct spike-and-recovery experiments with known contaminant concentrations
- Validate under controlled conditions that simulate environmental variability
- Perform inter-laboratory comparison where feasible
Research Reagent Solutions for Environmental Validation
Table 3: Essential Research Materials for Tiered Validation
| Reagent/Material | Function in Validation | Application Examples |
|---|---|---|
| Certified Reference Materials (CRMs) | Ground truth benchmark for model predictions | Soil/water CRMs with certified contaminant levels |
| Internal Standard Solutions | Quality control for analytical measurements | Isotopically-labeled analog contaminants for recovery studies |
| Performance Evaluation Materials | Blind testing of model accuracy | Synthetically contaminated samples with known concentrations |
| Field Sampling Kits | Representative sample collection | Standardized containers, preservatives, sampling protocols |
| Sensor Calibration Standards | Instrument performance verification | Standard solutions for calibrating analytical instruments |
Case Studies: Successes and Pitfalls
Digital Soil Mapping: The LPOCV Solution
A compelling case study in 3-dimensional digital soil mapping demonstrates the critical importance of appropriate validation methods. Researchers compared leave-sample-out cross-validation (LSOCV) versus leave-profile-out cross-validation (LPOCV) for predicting soil properties including cation exchange capacity, clay content, pH, and total organic carbon [38]. With augmented datasets, LSOCV generated accuracy metrics that were 29–62% higher than LPOCV, while for non-augmented data, LSOCV metrics were 8–18% higher [38]. This dramatic discrepancy shows how conventional validation can massively overestimate model performance when spatial autocorrelation exists.
Insulator Contamination Classification: Experimental Validation
In engineering environmental applications, researchers developed a comprehensive experimental validation for machine learning models classifying contamination levels of high-voltage insulators using leakage current [12]. By creating controlled datasets that included temperature and humidity variations, then extracting features from multiple domains, they achieved accuracies exceeding 98% with decision tree-based models [12]. This success highlights how rigorous experimental validation with environmentally relevant parameters establishes model reliability.
Drug Repurposing for Lipid Management: Multi-Tiered Approach
A pharmaceutical research example demonstrates the power of tiered validation across computational and experimental domains. Scientists employed machine learning to identify FDA-approved drugs with potential lipid-lowering effects, then implemented a multi-tiered validation strategy encompassing large-scale retrospective clinical data analysis, standardized animal studies, molecular docking simulations, and dynamics analyses [69]. This comprehensive approach confirmed that four candidate drugs, with Argatroban as the representative, demonstrated significant lipid-lowering effects [69].
Integration Pathway: Connecting Tiers for Robust Validation
The following diagram illustrates how the three validation tiers integrate into a cohesive workflow that connects technical, conceptual, and experimental elements:
Tiered validation strategies that integrate reference materials and environmental plausibility checks represent a paradigm shift in machine learning for environmental contaminant research. By addressing the critical problem of data leakage through spatial and temporal validation approaches like LPOCV, establishing biological plausibility through mechanistic reasoning, and verifying predictions with experimental validation using reference materials, researchers can develop models that are not only statistically sound but also environmentally relevant.
The future of ML validation in environmental science lies in developing more sophisticated approaches for assessing model performance under complex real-world conditions, creating standardized reference materials for emerging contaminants, and establishing validation frameworks that can adapt to rapidly changing environmental scenarios. As machine learning continues to transform environmental research, rigorous tiered validation will be essential for building models that policymakers and stakeholders can trust for critical decisions affecting ecosystem and human health.
In machine learning, particularly within scientific fields like environmental contaminant research, data leakage occurs when information from outside the training dataset is inadvertently used to create the model. This compromises the model's ability to generalize to new, unseen data and leads to significantly over-optimistic performance metrics [70]. The subsequent correction of this leakage often fundamentally alters claims about a model's superiority, revealing whether reported performance stems from genuine predictive power or from methodological flaws. This paper synthesizes evidence from diverse domains—including finance, clinical diagnostics, and digital soil mapping—to provide a comparative analysis of how leakage correction impacts assertions of model performance and superiority.
Quantitative Evidence of Leakage Impact
Data leakage artificially inflates model performance metrics, and its correction provides a more accurate, and often diminished, view of a model's true capabilities. The table below summarizes key quantitative findings from empirical studies across different fields.
Table 1: Quantitative Impact of Data Leakage Correction on Model Performance
| Domain / Study | Model/Task | Key Performance Metric | With Leakage | After Leakage Correction | Impact on Superiority Claims |
|---|---|---|---|---|---|
| 3D Digital Soil Mapping [38] | Prediction of soil properties (CEC, clay, pH, TOC) | Concordance Correlation Coefficient (CCC) | 29-62% higher (with data augmentation) | Baseline (after LPOCV) | LSOCV creates over-optimistic models; LPOCV is necessary for reliable validation. |
| Parkinson's Disease Diagnosis [71] | Multiple ML classifiers for early detection | Specificity | Superficially acceptable F1 scores | Catastrophic failure (most healthy controls misclassified) | High accuracy was due to leakage from overt diagnostic features, not genuine predictive power. |
| Financial Forecasting [72] | Machine Learning vs. Linear Models for stock returns | CAPM/FF3 Alpha | Claim of disappeared predictability | Strongly statistically significant alpha remained (-0.77%, p<0.1%) | ML model superiority claims remained valid post-leakage correction, contrary to initial critique. |
| LLM Benchmarking [70] | GPT-2 on a contaminated benchmark | Accuracy | 15 percentage points higher | Baseline (on uncontaminated set) | Artificially inflated scores create a false impression of model ability. |
The evidence demonstrates that the effect of leakage correction is not uniform. In some cases, it completely invalidates model utility (e.g., clinical diagnostics without valid features), while in others, a robust model's relative superiority persists despite inflated absolute performance [72] [71]. The core issue is that leakage undermines the reliability of performance metrics, making them uninformative about a model's real-world generalization [38].
Detailed Experimental Protocols for Leakage Correction
To ensure the validity of model superiority claims, researchers must implement rigorous experimental designs. The following protocols, drawn from the cited literature, provide methodologies for correcting and preventing data leakage.
Leave-Profile-Out Cross-Validation in 3D Mapping
In 3D digital soil mapping, a common source of leakage is the violation of independence between training and test sets due to vertical autocorrelation within soil profiles.
- Objective: To avoid contamination of the test dataset caused by vertical autocorrelation of soil properties from different samples within the same profile [38].
- Methodology:
- Identify all distinct soil profiles in the dataset.
- Instead of randomly splitting individual soil samples (Leave-Sample-Out CV, or LSOCV), partition the profiles into k folds.
- For each fold, use all samples from the held-out profiles as the test set, and all samples from the remaining profiles as the training set. This ensures no samples from the same profile are in both training and test sets simultaneously [38].
- Outcome Measurement: Compare accuracy metrics (e.g., CCC, RMSE) from LSOCV and LPOCV. The cited study found LSOCV inflated CCC metrics by 8-18% without data augmentation and by 29-62% with augmentation, demonstrating that LPOCV provides a realistic performance estimate [38].
Three-Way Data Split with Clinically-Grounded Feature Exclusion
In clinical ML, such as for early Parkinson's Disease (PD) detection, leakage often arises from using features that are themselves diagnostic criteria, which would not be available in a real-world pre-diagnostic scenario.
- Objective: To simulate a subclinical diagnostic scenario and evaluate the true predictive utility of models by excluding overt, diagnostic features [71].
- Methodology:
- Feature Exclusion: Prior to analysis, manually remove all features corresponding to overt motor symptoms (e.g., tremor, rigidity) and other clinically obvious indicators based on clinical knowledge, not automated selection. This prevents the model from "cheating" by using the answer [71].
- Three-Way Data Split:
- Training Set (80%): Used for model fitting and internal cross-validation.
- Validation Set (10%): Used for hyperparameter tuning and early stopping.
- Test Set (10%): Held out for final, unbiased evaluation. Splitting should use stratified random sampling to preserve class balance [71].
- Model Evaluation: Train multiple ML algorithms (e.g., SVM, Random Forest, XGBoost, DNN) and evaluate performance on the test set using metrics that reveal pathological behaviors, such as confusion matrices and specificity, not just aggregate F1 scores [71].
- Outcome Measurement: The cited study found that without overt features, models failed catastrophically, showing near-zero specificity. This confirmed that the high accuracy reported in many studies was due to data leakage rather than genuine predictive power for early detection [71].
Visualization of Leakage Correction Workflows
A rigorous methodology is essential for correcting data leakage. The following workflow, synthesizing best practices from multiple domains, provides a visual guide for researchers.
To effectively combat data leakage, researchers should be equipped with both conceptual frameworks and practical tools. The following table details key "research reagents" for ensuring robust model validation.
Table 2: Essential Reagents for Data Leakage Prevention and Correction
| Reagent / Resource | Type | Primary Function in Leakage Correction |
|---|---|---|
| Leave-Profile-Out Cross-Validation (LPOCV) [38] | Validation Technique | Prevents data leakage from spatially or temporally autocorrelated data structures (e.g., soil profiles, medical time series) by ensuring entire profiles/groups are in either training or test sets. |
| Three-Way Data Split [71] | Data Partitioning Protocol | Creates a dedicated validation set for hyperparameter tuning, preventing the test set from indirectly influencing the model building process and providing a final, unbiased evaluation. |
| Clinically-Grounded Feature Exclusion [71] | Feature Selection Protocol | Simulates real-world prediction scenarios by manually excluding features that would not be available at the time of prediction, preventing trivial solutions and testing genuine predictive power. |
| Confusion Matrix Analysis [71] | Diagnostic Visualization | Reveals pathological model behaviors (e.g., catastrophic failure in specificity) that are masked by aggregate metrics like accuracy or F1 score, which are often inflated by leakage. |
| Dynamic Benchmarks [70] | Evaluation Framework | Mitigates contamination in LLM evaluation by using test sets compiled from data published after the model's training cut-off, ensuring the model has not seen the test data. |
| Model Visualization Tools [73] | Diagnostic Tool | Provides insights into model structure (e.g., decision trees) and performance (e.g., ROC curves), aiding in the identification of potential overfitting and unrealistic performance. |
The correction of data leakage is not merely a technical formality but a fundamental process that validates or invalidates claims of model superiority. Evidence from diverse fields shows that leakage inflates performance metrics by 15% to over 60%, creating a false narrative of capability [38] [70]. While leakage correction can nullify claims in some contexts (e.g., clinical diagnostics using invalid features) [71], it can also reinforce them in others by demonstrating that a model's superior performance is robust and genuine [72]. For machine learning in environmental contaminant research and other scientific domains, the path forward requires a disciplined adherence to rigorous validation protocols, such as LPOCV for spatial data, clinically-grounded feature exclusion, and transparent reporting. Ultimately, the credibility of machine learning applications in high-stakes research hinges on this rigorous approach to preventing data leakage.
Machine learning (ML) has emerged as a powerful tool for tackling complex environmental challenges, including the prediction of atmospheric ozone pollution and the classification of contamination levels. However, the reliability of these models is critically dependent on the rigor of the benchmarking process. A prevalent yet often overlooked issue in environmental ML research is data leakage, where information from the test dataset inadvertently influences the model training process. This leads to overly optimistic and unreliable performance metrics, compromising the model's real-world applicability [38] [74]. This whitepaper examines key case studies in ozone prediction and classification, benchmarking model performance with a specific focus on methodologies that prevent data leakage. The objective is to provide researchers and scientists with a framework for developing accurate, robust, and generalizable ML models for environmental monitoring.
The Critical Challenge of Data Leakage in Environmental ML
Data leakage occurs when there is an inappropriate overlap between the data used for training a model and the data used for testing it. This can happen during data preprocessing, feature selection, or through non-independent data splitting, particularly when dealing with spatial or temporal autocorrelation [74].
In the context of 3-dimensional environmental data, such as vertical soil profiles or time-series air quality data, standard validation methods like Leave-Sample-Out Cross-Validation (LSOCV) can be problematic. When samples from the same profile or time series are split across training and test sets, the inherent autocorrelation allows the model to "learn" the test data structure, inflating performance metrics. A study on digital soil mapping demonstrated that LSOCV produced accuracy metrics (Concordance Correlation Coefficient) that were 29–62% higher than more rigorous methods when used with augmented data [38].
To ensure reliable benchmarking, Leave-Profile-Out Cross-Validation (LPOCV) is recommended. This method involves partitioning all samples from a single profile (or a monitoring station in time-series data) entirely into either the training or the test set. This practice effectively prevents data leakage caused by vertical or temporal autocorrelation and provides a more realistic estimate of a model's ability to generalize to new, unseen locations or time periods [38].
Case Study 1: Ozone Pollution Prediction
Experimental Protocols and Model Architectures
1. SHAP-IPSO-CNN Model: This integrated model combines a Convolutional Neural Network (CNN) with an Improved Particle Swarm Optimization (IPSO) algorithm and SHapley Additive exPlanations (SHAP) analysis.
- Data Input: Features include atmospheric pollutants (VOCs, NOx, SO2) and meteorological data (temperature, relative humidity, pressure). An atmospheric dispersion model (Gaussian plume) is first used to predict the concentration distribution of VOCs from emission sources at monitoring stations [75].
- Feature Optimization: The IPSO algorithm dynamically adjusts the model's training features based on their importance scores from SHAP analysis. The IPSO improves upon standard PSO by adaptively balancing global and local search capabilities and incorporating an adaptive learning rate mechanism [75].
- Model Validation: Performance is validated using R² (coefficient of determination), MAE (Mean Absolute Error), and RMSE (Root Mean Squared Error).
2. Random Forest (RF) with SHAP Analysis: This approach was used to unravel the seasonal effects of chemicals and meteorology on ground-level ozone.
- Data Input: Fine-resolution atmospheric composition measurements, including chemical-aerosol factors (VOCs, PM2.5, NOx) and meteorological drivers (air temperature, relative humidity) [76].
- Model Training: A Random Forest model is trained. The model's interpretability is enhanced using SHAP values to quantify the contribution of each input variable to the O3 predictions [76].
- Validation: Model performance is assessed using 10-fold cross-validation R² values.
3. Dynamic Machine Learning Models: This study compared nineteen machine learning models, emphasizing the use of time-lagged data.
- Data Input: Initial models used only weather conditions. Improved models incorporated pollution data (NO₂, SO₂, PM) and time-lagged measurements of ozone concentrations [77].
- Feature Selection: Random Forest-based feature selection was employed to identify the most influential variables [77].
- Model Comparison: Nineteen models were evaluated, including linear models, Support Vector Regression (SVR), Gaussian Process Regression (GPR), Multi-layer Perceptron (MLP), and ensemble methods [77].
Benchmarking Performance in Ozone Prediction
The following table summarizes the quantitative performance of various models and approaches from the case studies.
Table 1: Performance Benchmarking of Ozone Prediction Models
| Model / Approach | Dataset / Location | Key Performance Metrics | Notable Findings |
|---|---|---|---|
| SHAP-IPSO-CNN [75] | Chemical Industry Park, China | R²: 0.9492, MAE: 0.0061 mg/m³, RMSE: 0.0084 mg/m³ | Outperformed IPSO-CNN and SHAP-PSO-CNN models. |
| Random Forest (RF) [76] | Tucheng, Northern Taiwan | 10-fold CV R² > 0.867 | SHAP analysis revealed seasonal disparities in driver importance. |
| BP Neural Network [78] | Sichuan Province, China | Classification Accuracy: >80% for 14 out of 21 cities (single classifier) | A single classifier for 21 cities performed better than 12 regional classifiers. |
| Dynamic ML Models [77] | KAUST | 300% RMSE improvement vs. static models; 200% RMSE improvement vs. reduced models. | Incorporating time-lagged data was crucial for high accuracy. Best model computation time: 0.01 seconds. |
| Non-linear ML Model [79] | Lugano, Switzerland | MAE: 9 μg/m³ | Model based on NO₂, NOx, SO₂, NMVOC, temperature, and radiation. Simpler models could match ANN performance. |
Signaling Pathway and Workflow for Ozone Prediction
The following diagram illustrates a generalized and rigorous workflow for developing a machine learning model for ozone prediction, integrating steps to mitigate data leakage.
Case Study 2: Meteorological Condition Classification for Ozone Pollution
Experimental Protocol: BP Neural Network for Classification
This study focused on classifying meteorological conditions conducive to different levels of ozone pollution, rather than predicting continuous ozone concentrations [78].
- Data and Labeling: The study used surface hourly ozone (O₃) concentrations and meteorological data from 21 cities in Sichuan Province, China. Ozone pollution was divided into three discrete levels based on concentration thresholds, resulting in three corresponding groups of meteorological conditions.
- Input Features: The input parameters for the Back Propagation (BP) neural network were identified by evaluating the relationship between ozone and potential drivers. The selected features were: Relative Humidity, Temperature, Mixing Layer Height, Precipitation, and Nitrogen Dioxide (NO₂)
- Model Architecture and Training: Two experimental setups were used:
- 12 Individual Classifiers: Cities were grouped into 12 regions based on geography and sample size, with a separate BP classifier trained for each group.
- Single Classifier: One BP neural network model was trained for all 21 cities.
- Validation: Classification accuracy was calculated by comparing the model's output against observations [78].
Benchmarking Performance in Contaminant Classification
The performance of the classification approach is summarized below.
Table 2: Performance Benchmarking of BP Neural Network for Ozone Pollution Classification [78]
| Model Configuration | Classification Accuracy Results | Comparative Finding |
|---|---|---|
| 12 Individual BP Classifiers | All 21 cities: >60%18 cities: >70%9 cities: >80% | The single-classifier approach demonstrated superior and more consistent performance across the domain. |
| Single BP Classifier for 21 Cities | 20 cities: >60%18 cities: >70%14 cities: >80% |
The Scientist's Toolkit: Essential Research Reagents and Materials
For researchers replicating or building upon this work, the following table details key "research reagents" – the essential data types and computational tools required in this field.
Table 3: Key Research Reagents for ML-Based Ozone and Contaminant Research
| Reagent / Material | Function & Explanation | Example Usage |
|---|---|---|
| Atmospheric Dispersion Model | Predicts the transport and concentration of pollutants from emission sources to monitoring points, providing critical input features. [75] | Gaussian plume model used to estimate VOCs concentration from industrial parks at target monitoring stations. |
| SHAP (SHapley Additive exPlanations) | A game-theoretic method to interpret ML model outputs, quantifying the contribution of each feature to individual predictions. [76] [75] | Identifying NOx and temperature as the dominant drivers of high ozone concentrations in summer. |
| Improved PSO (IPSO) Algorithm | An optimization algorithm that enhances model performance by dynamically adjusting features and hyperparameters, improving global search efficiency. [75] | Optimizing the feature set and parameters of a Convolutional Neural Network (CNN) in the SHAP-IPSO-CNN model. |
| Time-Lagged Data | Previous measurements of target and feature variables used as model inputs to capture temporal dynamics and autocorrelation. [77] | Using ozone concentrations from the previous 6-24 hours to significantly improve the prediction of future levels. |
| Random Forest (RF) Algorithm | A versatile ensemble learning method used for both regression and classification tasks, and for determining feature importance. [76] [77] | Modeling ozone concentrations and selecting the most influential variables from a set of pollutants and meteorological factors. |
The case studies presented demonstrate that machine learning can achieve high performance in ozone prediction and classification, with models reaching R² values over 0.94 and classification accuracies exceeding 80%. However, these results are only meaningful if derived from rigorous benchmarking practices that explicitly account for and prevent data leakage. The use of LPOCV for spatial/temporal data, external validation on hold-out datasets, and interpretability tools like SHAP are not merely best practices but essential components of reliable environmental ML research. The presented workflows and toolkit provide a blueprint for researchers to develop models that are not only high-performing in a benchmark setting but also truly robust and generalizable for informing environmental policy and public health decisions.
Conclusion
Data leakage presents a formidable threat to the integrity and reproducibility of machine learning in environmental contaminant research. Synthesizing the key intents, it is clear that overcoming this challenge requires a multi-faceted approach: a solid foundational understanding of leakage types, meticulous methodological practices during model development, proactive troubleshooting via both manual and automated tools, and rigorous, multi-tiered validation against real-world environmental scenarios. Future progress hinges on the mutual inspiration between data science, mechanistic models, and laboratory fieldwork. For biomedical and clinical research, which increasingly relies on similar complex, high-dimensional data, the lessons from environmental science are directly transferable. Adopting these rigorous frameworks is essential for building predictive models that are not only statistically sound but also truly actionable for protecting human health and ecosystems, thereby closing the critical gap between analytical capability and reliable environmental decision-making.
References
- 1. What is Data Leakage in Machine Learning? [https://www.ibm.com/think/topics/data-leakage-machine-learning]
- 2. Data 'leaks' can sink machine learning models | Yale News [https://news.yale.edu/2024/02/28/data-leaks-can-sink-machine-learning-models]
- 3. The effects of data leakage on connectome-based machine ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10793416/]
- 4. A systematic review of data mining and machine learning for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5704396/]
- 5. Replication crisis [https://en.wikipedia.org/wiki/Replication_crisis]
- 6. The Reproducibility Crisis in Machine Learning [https://medium.com/@johnmunn/the-reproducibility-crisis-in-machine-learning-a-reckoning-a-reset-6edac20cdd34]
- 7. Common issues of data science on the eco-environmental ... [https://www.sciencedirect.com/science/article/pii/S0160412025000522]
- 8. Open science interventions to improve reproducibility and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11979971/]
- 9. Guest post: NIH-funded replication studies are not the ... [https://retractionwatch.com/2025/06/03/guest-post-nih-funded-replication-studies-reproducibility-crisis-preclinical-research/]
- 10. Is there a reproducibility crisis? on the need for evidence ... [https://kar.kent.ac.uk/110789]
- 11. Common issues of data science on the eco-environmental ... [https://pubmed.ncbi.nlm.nih.gov/39884250/]
- 12. Experimental validation of machine learning for ... [https://www.nature.com/articles/s41598-025-97646-4]
- 13. Computo - A Journal for Transparent and Reproducible ... [https://ropensci.org/blog/2025/11/06/computo-journal-reproducible-research-statistics-machine-learning/]
- 14. WATCH: Machine Learning Reproducibility Challenge 2025 [https://ai.princeton.edu/news/2025/watch-machine-learning-reproducibility-challenge-2025]
- 15. Machine learning for environmental justice: Dissecting an ... [https://www.sciencedirect.com/science/article/pii/S0048969724058868]
- 16. Mapping the Rise in Machine Learning in Environmental ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12567794/]
- 17. Artificial intelligence technology in environmental research ... [https://www.sciencedirect.com/science/article/pii/S0160412025005392]
- 18. Machine Learning Approach for Groundwater ... [https://www.mdpi.com/2073-4441/17/1/121]
- 19. Explainable machine-learning-based predictions of blood ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12627720/]
- 20. A double machine learning model for measuring the impact ... [https://www.nature.com/articles/s41598-024-62916-0]
- 21. MLOps for Green AI and Sustainable Machine Learning in ... [https://ctomagazine.com/mlops-for-green-ai/]
- 22. Cross Validation in Time Series [https://medium.com/@soumyachess1496/cross-validation-in-time-series-566ae4981ce4]
- 23. Using k-fold cross-validation for time-series model selection [https://stats.stackexchange.com/questions/14099/using-k-fold-cross-validation-for-time-series-model-selection]
- 24. The importance of data splitting in combined NOx ... [https://www.sciencedirect.com/science/article/pii/S0048969723003595]
- 25. A Spatio-Temporal Dataset for Satellite-Based Landslide ... [https://www.nature.com/articles/s41597-025-06167-2]
- 26. 5.10 Time series cross-validation | Forecasting [https://otexts.com/fpp3/tscv.html]
- 27. Time Series Cross-Validation [https://www.geeksforgeeks.org/machine-learning/time-series-cross-validation/]
- 28. Time-series high spatio-temporal resolution vegetation leaf ... [https://www.sciencedirect.com/science/article/pii/S1569843225003917]
- 29. Integrating non-target analysis and machine learning [https://www.nature.com/articles/s41545-025-00504-z]
- 30. TimeExpert: Boosting Long Time Series Forecasting with ... [https://arxiv.org/html/2509.23145v1]
- 31. Research Brief 364: Machine Learning Creates More ... [https://tools.niehs.nih.gov/srp/researchbriefs/view.cfm?Brief_ID=364]
- 32. in Machine Learning: A Guide | Medium Preventing Data Leakage [https://medium.com/geekculture/preventing-data-leakage-in-machine-learning-a-guide-51445af9fbaf]
- 33. How to Preprocess Data in Machine Learning: Best Techniques [https://morsoftware.com/blog/preprocess-data-in-machine-learning]
- 34. Training Preventing in AI Systems | Blog | Tonic.ai Data Leakage [https://www.tonic.ai/blog/prevent-training-data-leakage-ai]
- 35. Data splitting to avoid information leakage with DataSAIL [https://pmc.ncbi.nlm.nih.gov/articles/PMC11978981/]
- 36. Non-Targeted Analysis Research [https://www.epa.gov/chemical-research/non-targeted-analysis-research]
- 37. Non-targeted analysis (NTA) and suspect screening ... [https://www.nature.com/articles/s41370-023-00574-6]
- 38. The problematic case of data leakage: A case for leave- ... [https://www.sciencedirect.com/science/article/pii/S0016706125000618]
- 39. Identification of Groundwater Contamination Sources ... [https://www.mdpi.com/2073-4441/16/17/2449]
- 40. Groundwater contaminant source identification considering ... [https://www.sciencedirect.com/science/article/pii/S1674987123001998]
- 41. Data Leakage in 2025: Types, Causes, and 5 Defensive ... [https://www.venn.com/learn/dlp/data-leakage/]
- 42. An Event Causality Identification Framework Using ... [https://www.mdpi.com/2078-2489/16/1/32]
- 43. adaptive balancing of deep representation and causal effect ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12587697/]
- 44. A stacked ensemble machine learning model for the ... [https://www.frontiersin.org/journals/big-data/articles/10.3389/fdata.2025.1522578/full]
- 45. Causal and Predictive Modeling of Short-Horizon Market ... [https://arxiv.org/html/2510.22348]
- 46. Quantitative Data Analysis. A Complete Guide [2025] [https://www.6sigma.us/six-sigma-in-focus/quantitative-data-analysis/]
- 47. Leakage and the reproducibility crisis in machine-learning- ... [https://www.sciencedirect.com/science/article/pii/S2666389923001599]
- 48. Data Leakage in Machine Learning Models - Shelf.io [https://shelf.io/blog/preventing-data-leakage-in-machine-learning-models/]
- 49. Data leakage detection in machine learning code - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC11935776/]
- 50. Leakage and the Reproducibility Crisis in ML-based Science [https://reproducible.cs.princeton.edu/]
- 51. Colour Blindness & Colour Choices - CamBioc Teaching [https://cambiocteach.com/accessibility/colourchoice/]
- 52. Top 10 Code Analysis Tools in 2025 [https://cycode.com/blog/top-10-code-analysis-tools/]
- 53. The Best 6 Code Analysis Tools of 2026 [https://www.aikido.dev/blog/code-analysis-tools]
- 54. 7 Best Practices for Designing Automated Data Pipelines in ... [https://www.shakudo.io/blog/7-best-practices-for-designing-automated-data-pipelines]
- 55. Data pipeline architecture: A guide to better design [https://www.rudderstack.com/blog/data-pipeline-architecture/]
- 56. Choosing blocks for spatial cross-validation: lessons from a ... [https://www.frontiersin.org/journals/remote-sensing/articles/10.3389/frsen.2025.1531097/full]
- 57. A dissimilarity-adaptive cross-validation method for ... [https://www.sciencedirect.com/science/article/pii/S1574954125002961]
- 58. Combining K-fold cross validation with bayesian ... [https://www.nature.com/articles/s41598-025-23336-w]
- 59. Integrating machine learning models with cross-validation ... [https://www.sciencedirect.com/science/article/abs/pii/S0013935124008569]
- 60. Best Practices to Engineering Big Data Pipeline Architecture [https://groupbwt.com/blog/big-data-pipeline-architecture/]
- 61. The Ultimate Guide to Data Pipeline Tools in 2025 [https://firsteigen.com/blog/best-data-pipeline-tools/]
- 62. A holistic framework for integrated sustainability ... [https://www.sciencedirect.com/science/article/pii/S0959652624024272]
- 63. What Are the Challenges of Environmental Data Collection? [https://pollution.sustainability-directory.com/question/what-are-the-challenges-of-environmental-data-collection/]
- 64. Explainable machine-learning-based predictions of blood ... [https://www.nature.com/articles/s41598-025-24213-2]
- 65. Model Validation Techniques | TDS Archive [https://medium.com/data-science/model-validation-techniques-explained-a-visual-guide-with-code-examples-eb13bbdc8f88]
- 66. Cross Validation in Machine Learning [https://www.geeksforgeeks.org/machine-learning/cross-validation-machine-learning/]
- 67. Choosing the Right Model Validation Strategy: A Decision ... [https://www.statology.org/choosing-the-right-model-validation-strategy-a-decision-tree-approach/]
- 68. Biological plausibility in environmental health systematic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11897980/]
- 69. Integration of machine learning and experimental ... [https://www.nature.com/articles/s41401-025-01539-1]
- 70. An Overview of Data Contamination: The Causes, Risks ... [https://www.holisticai.com/blog/overview-of-data-contamination]
- 71. The Effect of Data Leakage and Feature Selection on Machine ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12383348/]
- 72. Reply to: "Man vs. Machine Learning Revisited" [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=5154044]
- 73. How to Do Model Visualization in Machine Learning? [https://neptune.ai/blog/visualization-in-machine-learning]
- 74. Machine Learning in Environmental Research [https://pubmed.ncbi.nlm.nih.gov/37384597/]
- 75. Assessment model of ozone pollution based on SHAP- ... [https://www.nature.com/articles/s41598-025-87702-4]
- 76. Using machine learning to unravel chemical and ... [https://www.sciencedirect.com/science/article/pii/S0160412025003186]
- 77. A comparison of machine learning methods for ozone pollution prediction | Journal of Big Data | Full Text [https://journalofbigdata.springeropen.com/articles/10.1186/s40537-023-00748-x]
- 78. A Machine-Learning-Based Classification Method for Meteorological Conditions of Ozone Pollution - Aerosol and Air Quality Research [https://aaqr.org/articles/aaqr-22-06-oa-0239]
- 79. Analysis and prediction of atmospheric ozone ... [https://www.frontiersin.org/journals/big-data/articles/10.3389/fdata.2024.1469809/full]